It should be obvious, but everyone seems to be making the same mistake.
HTTPS only works if you use it. Everywhere.
If you don’t use HTTPS everywhere, a bad guy can intercept an insecure request and prevent the user from reaching your secure site. HSTS is a good start to mitigating the threat of accidentally using an insecure link, but it only helps if you have an HSTS policy set for every domain you will be using.
There’s a big collection of failures to use HTTPS here, but the following are ongoing problems that I’ve been complaining about for a long time now…
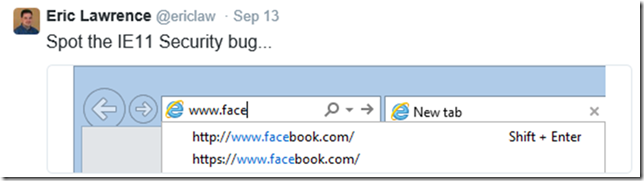
IE’s “Domain Suggestions” feature can prioritize insecure suggestions over secure suggestions:
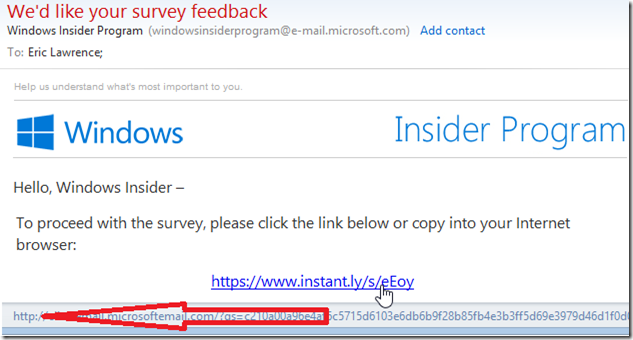
Many major companies (including OS vendors, investment firms, etc) offer HTTPS links in their email… Except they’re not really HTTPS; they’re HTTP links to a “click counter” that is meant to redirect to the secure link. These redirects can be intercepted:
Microsoft OneDrive’s Sharing experience generates secure links by default:
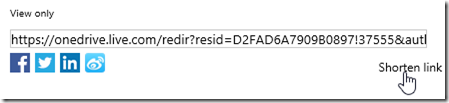
…but the link is made insecure if you click the “Shorten link” button:

The IE Team still hasn’t changed the default Bing search provider to use HTTPS:
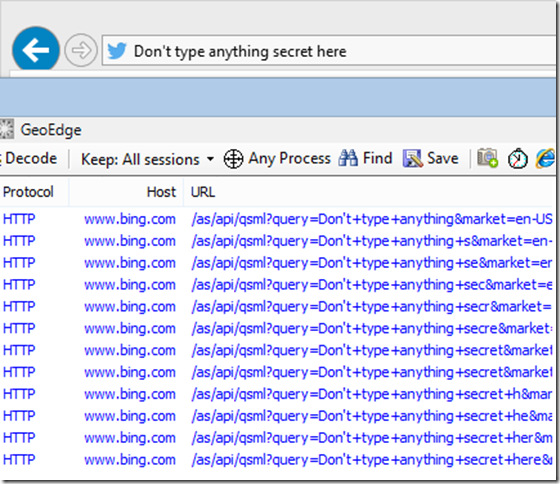
Surprisingly, both the Google and Yahoo providers offered are secure, and the Bing provider is secure in Firefox and Chrome. Only IE+Bing is insecure.
The list, sadly, goes on and on.
One of the more esoteric problems I’ve seen is on a site that generally does security quite well: Twitter.
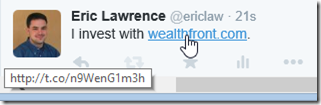
Consider what happens if a user posts a tweet: “I invest with wealthfront.com.” Now I, as a normal human, didn’t spell out https:// in front of that link and Twitter sees it as http://wealthfront.com. This, in itself, might be okay, because WealthFront.com sends a 24 month HSTS policy with the preload attribute, meaning that many browsers will automatically upgrade any http:// reference to https://. That’s great.
Except.
Twitter has some interesting logic in their site. They use a redirector (t.co) to rewrite all hyperlinks, presumably so they can track clicks and block spam or dangerous URLs. When you paste a link into Twitter, it looks to see if the link is to a HTTP target or to a HTTPS target. If it’s to a HTTP target, they use http://t.co and if it’s to a HTTPS target, they use https://t.co.
And here we find the problem. My innocent wealthfront.com reference, which should have been protected by HSTS, has been made insecure because the Twitter folks decided not to use HTTPS everywhere.
Update: They fixed this, now all t.co links are HTTPS.
If you think you’re smart enough not to use HTTPS everywhere, you’re probably wrong.
-Eric
Uhm… Maybe your blog itself should be served over https too then…
Indeed, it should. I’m currently talking to WordPress.com about this topic, as they use HTTPS on their own subdomains, but do not permit it for paid accounts that use non-Wordpress domains.