By far, the most commonly-reported “vulnerability” reported to the Chrome Vulnerability Rewards program boils down to “I can steal my own password.” Despite having its very own FAQ entry, this gets reported to the VRP at varying levels of breathlessness, sometimes multiple times per day.
You can see this “attack” in action:
Yes, it’s true, you can use Chrome (or Edge, or Firefox) to steal your own password.
-Eric
FAQ: What about Password-Stealing software?
PS: “But… but… what if I don’t want to use this easy trick and instead decide to steal my own passwords from myself by installing some software on my own PC? Isn’t that a security bug?”
No, although “Software can read passwords if I give it full permission to run on my computer” is probably the third or fourth most common non-bug reported to Chromium’s Security@ alias. crbug.com/678171 is one of many such filings.
FAQ: What about Group Policy lockdowns?
“But… but… what if I’m a clever admin and I don’t allow my users to use the Developer Tools or run arbitrary software. Am I safe then?” Well, no. The user can enter JavaScript in the Omnibox/Address bar, or use the Settings page to view or export passwords to a file.
PPPS: “What about the “Reveal Password” (eye) icon shown in Microsoft Edge? Can that expose an autofilled password?” No.
FAQ: What about “Require A Password To Fill Passwords”?
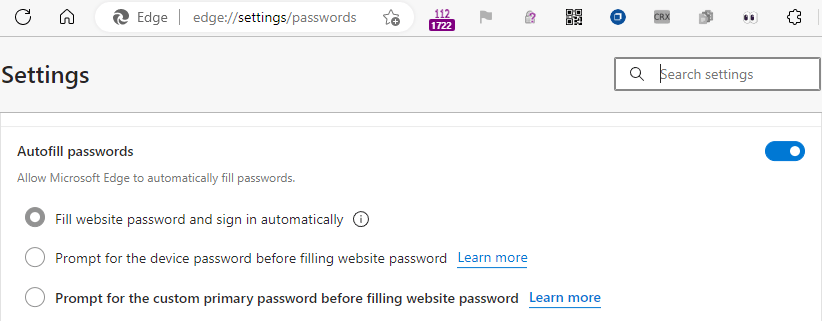
Edge offers a setting (on edge://settings/passwords) to control the behavior of auto-fill, but this is a speed-bump, not a security boundary. A user with unrestricted access to your logged-in user account can still grab passwords via slightly more cumbersome means.
Chromium uses encryption when storing passwords in almost all cases. However, the browser itself has the decryption key (necessarily). You can read more about why an attacker who has physical access or has compromised your machine is outside of the browser’s threat model in two of my blog posts: