You should enable “2-Step Verification” for logins to your Google account.
Google Authenticator is an app that runs on your iOS or Android phone and gives out 6 digit codes that must be entered when you log in on a device. This can’t really prevent phishing (because a phishing page will just ask you for a code from it and if you’re fooled, you’ll give it up) but it does prevent attacks if a bad guy has only your password. Authenticator is free and simple to use, and is supported by many sites, including GitHub. Microsoft offers a nearly identical Authenticator app too. How ToTP works.
YubiKeys (and similar) are small USB keys that you can configure your accounts to require. They are cheapish (~$18) and cannot be phished (even if you tap your key while on a phishing site, the attacker cannot use it due to how the crypto works). These are the best protection for your accounts (Googlers all use them) and are highly recommended for Chrome extension developers, journalists, activists, etc, etc.
Consider, for instance, this phishing email that this Chrome Extension developer received:
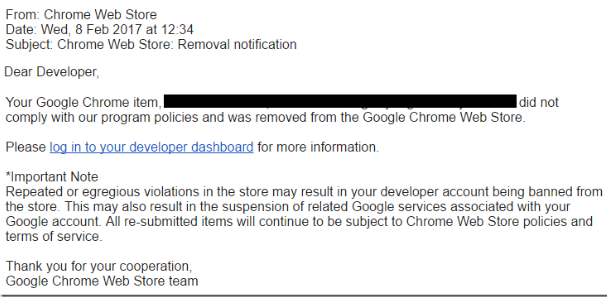
If the developer’s account were protected by a Yubikey, his credentials would be useless to a phisher because they would not have the required second factor necessary to log in and plant their malicious code in the developer’s extensions.
If the developer’s account were protected by a TOTP/Google Authenticator, it would require that the attacker collect the token value and be actively watching for victims such that the ephemeral token did not expire before they had a chance to replay it to the legitimate Google servers.
I often consider a 2FA “fobble” (?!) but the issue (that is not yet solved) is what to do when you loose it or it stops working.
Depending on the service you are either screwed if you 2FA becomes unusable, or the service provides alternatives like Google Authenticator, SMS, email, backup codes. In which case why not use one of those.
When it comes to authenticators it’s the same issue as a keyfob (!?), what if it doesn’t work, the phone get stolen, I know there is a “compatible” authenticator you can run on your desktop which makes it easy to duplicate it’s key storage, but again depending on the service you may be screwed if something happens.
Not getting access at all may be just as much a problem as the wrong person getting access. But let’s say we are lucky (?) with the service and they offer fallbacks like SMS, email, backup codes. Google does this. But in this case if the fallbacks still work why not just use them (SMS or email) as your 2FA.
And the reason I’m not bothering with backup codes is that I use a password manager with extremely long and generated passwords. I’d want to use backup (or secondary codes) but if a service is compromised such that the passwords are gained (which means they where stored as plaintext rather than using bcrypt or argon2id) then the backup codes (if the service offers this at all) is most likely compromised as well.
And if the passwords are not gotten but the login is compromised then the attacker will get the plaintext password regardless of how securely they are hashed on the server.
Sure I may be more vulnerable to phishing with the lack of a proper 2FA, but as long as I don’t get phished an attacker can only attempt to guess a randomly generated password which takes ages if online and is pretty much pointless if offline (and the hash is bcrypt or argon2id).
I do however have email or SMS “verification” checks that occur rarely with Microsoft and Google accounts, this happens rarely, or if I use a new device, these are not 2FA obviously.
As mentioned I might use a desktop 2FA authenticator at some point (shame there are so few good and simple open source ones, maybe I’ll just code my own). But I may also (as you mentioned extension developers etc) just make a separate “developer” account, with a password manager this is very easy to handle (I prefer offline password manager that is possible to backup the encrypted database manually).
It’s a shame no international services (like Google and Microsoft) support BankID (a scandinavian 2FA) which pretty much everyone in Norway has (or has available) through their bank. If something happens with that 2FA you can block it and get a new one (and you’ll have to identify yourself with a ID in person before you are handed your new 2FA).
This reduces the risk of impersonation and has a way to handle the loss of a 2FA without locking you out forever.
I don’t see why large international organizations/companies can’t have some way for users to locally ID themselves and get a 2FA (or get their 2FA activated/reset). Making a deal with postal offices might work as they require ID for recommended mail. One way to do it could be as simple as clicking a button on the service to issue/reset the 2FA, be given one half of a code and a reference number then go to the post office with your 2FA reference number (so the employee will never see the first part of the code), ID yourself and they print you the second half of a code, then go home and enter the full code into you 2FA thingy (on the same device), and that’s it.
Here is a interesting post regarding weaknesses of recovery options https://www.reddit.com/r/yubikey/comments/9n2ggc/be_wary_that_even_if_you_remove_other_recovery/