This post is intended to collect a random set of questions I’ve been asked multiple times about the new Chromium-based Edge. I’ll add to it over time. I wouldn’t call this a FAQ because these questions, while repeated, are not frequently asked.
Last Update: Sept 25, 2024
Can I get a list of all supported command-line arguments for msedge.exe?
Unfortunately, not easily. See my post on Edge Command Line Arguments.
Why does Edge ignore the command-line argument I passed it?
Why does Edge ignore the command-line arguments I passed it?
Usually, this happens because Edge was already running and your new invocation simply activated/showed the existing running instance (even if it was a hidden instance using Startup Boost). See my post on Edge Command Line Arguments.
Can an Enterprise Administrator use Group Policy to specify specific flags or command line arguments for all users?
No, this isn’t possible. Such a feature would be relatively easy for the Edge team to build, but would be impossible to support. Most Edge flags and many command-line arguments are basically “experimental”, existing only for troubleshooting purposes, not for use in production.
Flags and command-line arguments can be changed or removed at any time, and an Enterprise relying upon them is almost guaranteeing themselves an unpleasant surprise in the future.
If an enterprise finds that they have a strong need to control a given flag in their environment, they should file a support case with Microsoft requesting that the flag be promoted to a Group Policy controlled setting.
Why do I see msedge.exe in Task Manager when Edge isn’t visible?
Startup Boost enables the browser to launch more quickly. You can disable it if you like.
Can I block my employees from using the edge://flags page?
Update: Edge 93 introduces a new FeatureFlagsOverrideControl policy.
You can add edge://flags to the URLBlocklist if desired. Generally, we don’t recommend using this policy to block edge://* pages as doing so could have unexpected consequences.
Note that, even if you block access to edge://flags, a user is still able to modify the JSON data storage file backing that page: %LocalAppData%\Microsoft\Edge\User Data\Local State using Notepad or any other text editor.
Similarly, a user might specify command-line arguments when launching msedge.exe to change a wide variety of settings.
Can I block resources from a specific site without using an extension?
The URLBlocklist policy allows blocking navigation to specified URL patterns in either the top-level page or in subframes. It does not, however, prevent the specified resources from being loaded as assets in the page via <img>, <video>, <script>, fetch(), etc.
This policy also does not block URL changes via the JavaScript pushState API. This can have some surprising implications. This limitation, which applies to many URL-controlling features, means e.g. if you allow any chrome://settings link, a user can load that page and use the hyperlinks in the page to access other settings inside chrome://settings because clicking those links calls pushState rather than performing a normal navigation subject that would be subject to the policy.
Can I disable certain HTTPS ciphers?
The new Edge, like all Chromium-based browsers, uses BoringSSL for HTTPS connections. Because the new Edge no longer uses Windows’ SChannel (except for IEMode tabs), none of the prior SChannel cipher configuration policies or settings have any effect on the new Edge.
For administrators who wish to disable one or more ciphers, Edge offers a TLSCipherSuiteDenyList Group Policy. In contrast, Chrome explicitly made a design/philosophical choice (see this and this) not to support disablement of individual cipher suites via policy.
Ciphersuites in Edge may also be disabled using a command-line flag:
msedge.exe --cipher-suite-denylist=0x000a https://ssllabs.com
A few other notes:
- You can easily see what cipher suites your browser offers by visiting this page.
- The cipher suite in use is selected by the server from the list offered by the client. If an organization is worried about ciphers used within their organization, they can simply direct their servers to only negotiate cipher suites acceptable to them.
- The Chrome team has begun experimenting with disabling some weaker/older ciphersuites; see crbug.com/658905. For instance, 3DES is no longer available as of version 93.
- If an Enterprise has configured IE Mode, the IE Mode tab’s HTTPS implementation is still controlled by Internet Explorer / Windows / SChannel policy, not the new Edge Chromium policies.
- If TLS/1.3 is enabled, you cannot use the cipher-suite-denylist to disable ciphers 0x1301, 0x1302, and 0x1303. TLS1.3 spec: “A TLS-compliant application MUST implement the TLS_AES_128_GCM_SHA256 [GCM] cipher suite and SHOULD implement the TLS_AES_256_GCM_SHA384 [GCM] and TLS_CHACHA20_POLY1305_SHA256 [RFC8439] cipher suites (see Appendix B.4).”
- Edge on iOS uses TLS cipher implementations provided by Apple because the Edge browser (like all popular browsers) is just a wrapper around Safari’s WKWebView control.
- From time-to-time, browsers experiment with new ciphersuites. For instance, Chrome and Edge are interested in post-quantum key exchanges (where the key is exchanged in a way that is believed to be robust against quantum computers) and have experimented with new ciphersuites that offer such protections.
Can I use TLS/1.3?
TLS/1.3 is supported natively within the new Chromium-based Edge on all platforms.
Chromium-based Edge does not rely upon OS support for TLS. Windows’ IE 11 and Legacy Edge did not support TLS/1.3 in Windows 10 until recently, and now support TLS/1.3 in Windows 11.
For the time being, enabling both TLS/1.3 and TLS/1.2 is a best practice for servers.
Can I turn off TLS/1.3?
For testing purposes, you can set the SSLVersionMax command line argument to disable TLS/1.3, but the associated Group Policy was removed in Chromium 75 because there should be no need to do this in general.
msedge.exe --ssl-version-max=tls1.2 https://ssllabs.com
Can Extensions be installed automatically?
Enterprises can make extension install automatically and prevent disabling them using the ExtensionInstallForcelist Policy. Admins can also install extensions (but allow users to disable them) using the ExtensionSettings policy with the installation_mode set to normal_installed.
Here are the details to install extensions directly via the Windows Registry. Please note that if you want to install extensions from the Chrome WebStore, then you must provide the Chrome store id and update url: https://clients2.google.com/service/update2/crx.
Can specific file types be set to auto-open? Can I change my mind?
After downloading a file, you can click the “…” menu next to the download item and choose “Always open files of this type” from the context menu:

This option is not available for all file types (e.g. file types deemed dangerous cannot be auto-opened).
One challenge with this UI is that after you set this option, the download bar will not be shown for this file type any longer, leaving you no way to untick the “Always open files of this type” menu item.
The secret to changing your mind is to visit edge://settings/downloads and click the Clear all button next to the File types which are opened automatically after downloading list. There is no way to clear just one file type from the list short of editing the profile’s PREFERENCES json directly.
Presently, no Group Policy is available to force file types (except PDF) to open automatically, but this is a common enterprise request. The Master Preferences file can be configured with this option, but those defaults are only used when creating new browser profiles, and users may change them.
Can I go directly to single-word (Intranet) sites without doing a search first?
Can I avoid doing a search with a notification bar saying “Did you mean to go to <http://payroll>?” In Internet Explorer, there was a “Go to an intranet site for a single word entry in the Address bar” checkbox in the Advanced Settings.
Use the GoToIntranetSiteForSingleWordEntryInAddressBar policy to change the default behavior.
How can I get PDFs to open outside of Edge?
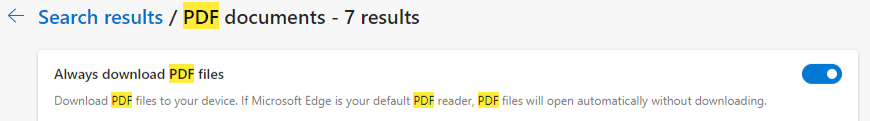
By default, Edge will attempt to render any PDF (navigating to a PDF will not be considered a “Download”) unless you tell Edge not to. To make this change, set your Windows settings so that you have a non-Edge app selected as your PDF reader. Then, inside edge://settings, tick this option:
The setting’s title is Always download PDF files but a more informative title would be Open PDF files using the Windows-default handler for PDF files. If your Windows-default handler for PDF files is Edge, then the file will not be "downloaded" and will instead render inline inside Edge. But if your Windows-default handler for PDF files is not Edge, then navigations to a PDF file will be treated as Downloads and clicking the "Open" link for a PDF in the Download Manager will open the PDF in the Windows-default handler application. But that’s obviously too long for a title. :)
Why does Edge Dev/Canary sometimes show red in unexpected places?
Chromium uses bright red as its “color not found” fallback; this has the upside and downside of quickly drawing a lot of attention to this class of bug.
When upstream Chromium makes a change in the color tables that Edge fails to fix up in our pump before the next build is released, it results in elements taking on a red color until we fix the oversight.
Can I use URLs of unlimited size?
Within Chromium, URLs of up to 2mb can be used in general, although some UI surfaces will truncate URLs at 32kb. For performance and reliability reasons, I would not recommend using URLs over 8k in length.
- When invoking an application protocol handler, urls are limited to 2048 characters.
- Pages running in IE Mode remain limited to the old IE length limit— using >
2083characters is unreliable. - Some websites and security products will fail in surprising ways if they receive URLs over a certain length.
Can I use configure Edge to use more than 6 HTTP/1.1 connections per host?
No. Using parallel connections as was common in HTTP/1.1 suffers from lower performance and increased load on the server. As a hacky workaround to exceed the typical 6 connections-per-host limit, some sites use “sharding” which assigns multiple DNS names to a single server. Because browser connection limits are based on the hostname, this allows the client to make 6*NumShards parallel connections.
Chromium exposes only a policy to control the maximum connections per proxy server, but there is no policy to control the maximum connections per web server. This sometimes leads to problems in niche scenarios, but we have not, as yet, heard a non-trivial number of complaints.
Note that things will get a bit more complex in the future due to security/privacy partitioning; when PartitionConnectionsByNetworkIsolationKey is enabled, the connections-per-host limit is enforced against each partitioned socket pool. If pages from a.example and b.example both use resources from example.net, each page can use six connections to example.net due to the partitioning of the connection pool by the Network Isolation Key.
In the ideal case, the site would deploy HTTP/2 or HTTP/3, which multiplex many (Chromium default 100, server configurable to up to 256) requests over a single TCP/IP connection, eliminating head-of-line blocking and providing much better performance vs. legacy HTTP/1.1. Chrome’s WebSocketsPerHost limit is 255.
Can I use Group Policy to turn off HSTS for specific sites?
No. There is no policy that turns of HSTS for a host that had requested it.
The HSTSPolicyBypassList policy description led users to believe it does something it does not. I fixed a bug to get the text clarified. The policy should read something like:
Setting the policy specifies a list of hostnames that bypass preloaded HSTS upgrades from http to https. Only single-label hostnames are allowed in this policy, and the policy applies only to HSTS-preloaded “static” entries (“app”, “new”, “search”, “play”, etc”). This policy does not prevent HSTS upgrades for servers that have explicitly requested HSTS upgrades using the Strict-Transport-Security response headers. Supplied hostnames must be canonicalized: Any IDNs must be converted to their A-label format, and all ASCII letters must be lowercase. This policy only applies to the specific single-label hostnames specified, not to subdomains of those names.
Some users complain that they’re getting HSTS for localhost sites and try to use this policy to prevent that. localhost is not on the HSTS Preload list. If your browser is HSTS-upgrading localhost, it’s because it received a Strict-Transport-Security response header from localhost that turned on HSTS. To fix that:
- Stop sending the header
- On
edge://net-internals/#hsts, use the Delete domain security policies section to removeLocalhost - Or you can hit
Ctrl+Shift+Deleteto open the Clear Browsing Data dialog and chooseCached Images and Files. This will delete ALL dynamic HSTS rules.
Update: I wrote an extension that will disable HSTS on all https://localhost responses.
Can I control Permissions (like Allow Popups) based on the Site’s IP address?
The Permissions system’s “Site Lists” feature does not support specifying an IP-range for allow and block lists.
It does support specification of individual IP literals, but such rules are only respected if the user navigates to the site using said literal (e.g. http://127.0.0.1/). If a hostname is used (http://localhost), the IP Literal rule will not be respected.
How does visiting a site in Internet Explorer open Edge automagically?
Edge installs a Browser Helper Object into Internet Explorer with a pre-provisioned site list.
Other than that, a site can try to launch a link using the microsoft-edge: URL protocol.
How does Edge render Office documents directly in the browser?
The OpenInOfficeViewerIfApplicable feature watches navigations to detect when Office-related file extensions (.xls, .docx, pptx, etc) or Content-Types (application/msword, application/vnd.ms-excel, etc) are observed, indicating that a navigation led directly to an Office document that would otherwise be deemed as having a non-webby MIME type and thus normally be converted into a download.
The feature is bypassed if:
- The
Open Office files in the browsercheckbox is turned off inedge://settings - The response contains a
Content-Disposition: attachmentheader - The request contains an
AuthorizationorProxy-Authorizationheader. - The user initiated the download from the “Save As” item on the browser’s context menu
- The referring URL is on a limited set of exempted domains (Office, SharePoint, OneDrive, Blackboard, etc)
- The request method is not
GET - The file size is not known (e.g.
Transfer-Encoding: chunked) - The file size is over 100mb
- The browser is running in Incognito mode
- The file was served from an IP address that is not publicly routable
Can I turn off cross-origin security in Edge?
You shouldn’t.
The flag --disable-web-security command line flag is not supported (that is to say, we won’t guarantee what it does or does not allow, and it could disappear at any time), and hasn’t been updated to account for all of the various security features added to the browser over the last few years (see https://crbug.com/1150447). Launching the browser with this flag makes that browser instance inherently unsafe to use. That was also true of the old “Access data sources” flag in IE, although the IE-flag was at least Zone-limited.
The command must be paired with a user-data-dir argument:
msedge.exe --disable-web-security --user-data-dir=C:\temp example.com
Developers should fix the dependent target sites to emit proper Access-Control-Allow-Origin headers so that the web’s same-origin-policy is respected.
If they do not control the target site, they will need to build a server proxy (browser->their-server->remote-server) that sets the correct ACAO headers.
Can I change the browser’s User-Agent string?
Edge allows configuration of a UA string via the Developer Tools or the --user-agent command line argument. It does not support customization of the UA string via a plain setting or Group Policy.
Browser extensions can be installed to spoof the UA string.
Generally, we do not believe that changing the UA string for day-to-day browsing is a good idea—it typically ends up causing more problems than it solves.
How do I ensure WebDriver is up-to-date?
Some folks use a third-party solution such as WebDriverManager which automatically maintains browser drivers for every major browser including Edge. Some prefer to write their own scripts that check the Edge browser version before running tests, downloading the matching driver from the Edge WebDriver Directory. An example script written in Python can be found here.
Does Edge support Chrome Apps?
Edge has never supported the non-standard Chrome Apps platform, because this platform was originally slated for deprecation back in 2019. The Microsoft Web Store does not allow Chrome Apps, and Chrome Apps were never installable into Edge from the Chrome Web Store.
We recently learned that some users were side-loading Chrome Apps into Edge; these will stop working soon when Chrome disables the Apps platform. Developers of Chrome Apps should migrate to modern standards-based code now.
Can I sync/transfer my Automatic Profile Switch settings?
As of Edge 109, not yet, no, settings for automatic switching are not synced or exportable.
Will Chromium certificate-verification changes impact Edge?
Chromium is changing the way that Certificate Verification works; in the old days (on Windows at least), Chromium would ask the underlying operating system to validate that the certificate presented by a website is valid.
That’s changing in early 2023. You can read the details here, but the tl;dr is that there’s new certificate verification code (you shouldn’t notice any difference vs the old CAPI), and the same Windows trusted root list is used, but, carried within the browser itself.
Edge, regardless of bitness, installs to the Program Files (x86) folder. Why?
On 64-bit versions of Windows, 32-bit applications are meant to be placed into a C:\Program Files (x86)\ folder while native 64-bit applications are meant to be placed within the C:\Program Files\ folder. This enables side-by-side installation of applications that are available in both bitnesses (e.g. Internet Explorer 9 could run as either 32bit or 64bit). Windows folder names reflect this convention but have no actual impact on the bitness of the executables within.
Originally, Chromium was only available as a 32bit Windows executable installed to the X86 version of the folder. Even after 64bit versions became available and later became the default, the installation folder path was not updated for many years because there was no compelling reason to bother.
Relatively recently, Chrome changed to start installing to the “correct” folder, but for obscure reasons, Edge didn’t take this change.
Can I load legacy content designed for Internet Explorer?
In some cases, you may need to load content that only runs correctly in the crufty old Internet Explorer engine (e.g. a page that uses an ActiveX control).
The supported way to do this is IEMode in Edge. You should be very careful when loading content in IEMode because Internet Explorer code is old and considerably less secure than Edge mode; an attacker will find it much easier to attack your computer if you load their page in IEMode. IEMode runs with the comparatively weak Protected Mode sandbox, vs. the much stronger Chromium sandbox.
Standalone IE was deprecated in early 2023 and attempts to launch iexplore.exe are redirected to launch Edge instead. In most cases, this is a major improvement, but if you’re doing something exotic (like answering legacy browser UX trivia questions like me) you might need to occasionally run the old standalone UI. For the time being, at least, you can use this (afaik, unsupported) workaround. Save the following as IE.vbs:
Set IE = CreateObject("InternetExplorer.Application")
IE.Navigate "https://example.com"
IE.Visible = trueRun the script to get a standalone IE window. Be very careful as all of the security concerns noted above apply.
Is there any sort of “changelist”? Can I get advance notice of changes?
Generally, your best bet is to use a practical time machine and test your site in a pre-Stable channel like Dev or Canary.
That said, platform breaking changes of the most interest are noted on the site-impacting-changes page. Edge inherits nearly all of Chromium’s web platform changes, which they document more comprehensively on Chrome Status.
-Eric