Uneven Protection
Attacks flow like water: if you have a hole in your defenses, attacks will flow through that hole. Unless they’re trying to win a prize or show off, attackers do not bother attacking where your security posture is strongest.
Making your tallest wall taller usually isn’t useful.

Encryption
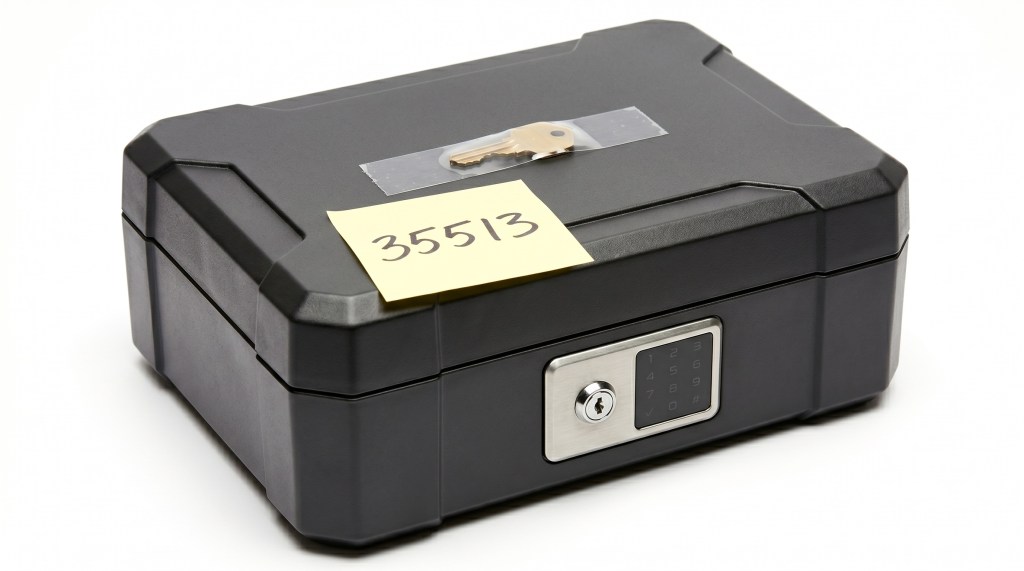
Security folks love encryption, for good reason. Proper encryption provides confidentiality (your secrets are secret) and integrity (no one can modify your encrypted data). The problem is that encryption is based on a secret key, and if you don’t protect that key, you likely haven’t done much of consequence. Effectively protecting the key is very difficult.
Enclaves
Enclaves provide a secure location to operate on secrets. Unfortunately, many implementations of secure enclaves are naive and provide no meaningful protection. One common problem is that the enclave acts as a confused deputy, fully willing to satisfy the requests of any attacker.
