If you offer web developers footguns, you’d better staff up your local trauma department.
In a prior life, I wrote a lot about Same-Origin-Policy, including the basic DENY-READ principle that means that script running in the context of origin A.com cannot read content from B.com. When we built the (ill-fated) XDomainRequest object in IE8, we resisted calls to enhance its power and offer dangerous capabilities that web developers might misconfigure. As evidence that even experienced web developers could be trusted to misconfigure almost anything, we pointed to a high-profile misconfiguration of Flash cross-domain policy by a major website (Flickr).
For a number of reasons (prominently including unwillingness to fix major bugs in our implementation), XDomainRequest received little adoption, and in IE10 IE joined the other browsers in supporting CORS (Cross-Origin-Resource-Sharing) in the existing XMLHttpRequest object.
The CORS specification allows sites to allow extremely powerful cross-origin access to data via the Access-Control-Allow-Origin and Access-Control-Allow-Credentials headers. By setting these headers, a site effectively opts-out of the bedrock isolation principle of the web and allows script from any other site to read its data.
Evan Johnson recently did a scan of top sites and found over 600 sites which have used the CORS footgun to disable security, allowing, in some cases, theft of account information, API keys, and the like. One of the most interesting findings is that some sites attempt to limit their sharing by checking the inbound Origin request header for their own domain, without verifying that their domain was at the end of the string. So, victim.com is vulnerable if the attacker uses an attacking page on hostname victim.com.Malicious.com or even AttackThisVictim.com. Oops.
Vulnerability Checklist
For your site to be vulnerable, a few things need to be true:
1. You send Access-Control-Allow headers
If you’re not sending these headers to opt-out of Same-Origin-Policy, you’re not vulnerable.
2. You allow arbitrary or untrusted Origins
If your Access-Control-Allow-Origin header only specifies a site that you trust and which is under your control (and which is free of XSS bugs), then the header won’t hurt you.
3. Your site serves non-public information
If your site only ever serves up public information that doesn’t vary based on the user’s cookies or authentication, then same-origin-policy isn’t providing you any meaningful protection. An attacker could scrape your site from a bot directly without abusing a user’s tokens.
Warning: If your site is on an Intranet, keep in mind that it is offering non-public information—you’re relying upon ambient authorization because your sites’ visitors are inside your firewall. You may not want Internet sites to be able to be able to scrape your Intranet.
Warning: If your site has any sort of login process, it’s almost guaranteed that it serves non-public information. For instance, consider a site where I can log in using my email address and browse some boring public information. If any of the pages on the site show me my username or email address, you’re now serving non-public information. An attacker can scrape the username or email address from any visitor to his site that also happens to be logged into your site, violating the user’s expectation of anonymity.
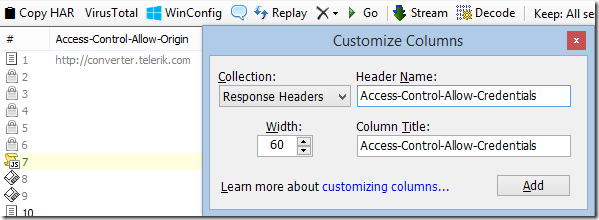
Visualizing in Fiddler
In Fiddler, you can easily see Access-Control policy headers in the Web Sessions list. Right-click the column headers, choose Customize Columns, choose Response Headers and type the name of the Header you’d like to display in the Web Sessions list.
For extra info, you can click Rules > Customize Rules and add the following inside the Handlers class:
public static BindUIColumn("Access-Control", 200, 1)
function FillAccessControlCol(oS: Session): String {
if (!oS.bHasResponse) return String.Empty;
var sResult = String.Empty;
var s = oS.ResponseHeaders.AllValues("Access-Control-Allow-Origin");
if (s.Length > 0) sResult += ("Origin: " + s);
if (oS.ResponseHeaders.ExistsAndContains(
"Access-Control-Allow-Credentials", "true"))
{
sResult += " +Creds";
}
var s = oS.ResponseHeaders.AllValues("Access-Control-Allow-Methods");
if (s.Length > 0) sResult += (" Methods: " + s);
var s = oS.ResponseHeaders.AllValues("Access-Control-Allow-Headers");
if (s.Length > 0) sResult += (" SendHdrs: " + s);
var s = oS.ResponseHeaders.AllValues("Access-Control-Expose-Headers");
if (s.Length > 0) sResult += (" ExposeHdrs: " + s);
return sResult;
}
-Eric
One note on Origin checking (and I’ve been burned by this before), it is *not* enough to simply check that the value ends with your domain name. “maliciousvictim.com” ends with “victim.com” but can obviously be registered independently.