In order to be eligible for the HSTS Preload list, your site must usually serve a Strict-Transport-Security header with an includeSubdomains directive.
Unfortunately, some sites do not follow the best practices recommended and instead just set a one-year preload header with includeSubdomains and then immediately request addition to the HSTS Preload list. The result is that any problems will likely be discovered too late to be rapidly fixed– removals from the preload list may take months.
The Mistakes
In running the HSTS preload list, we’ve seen two common mistakes for sites using includeSubdomains:
Mistake: Forgetting Intranet Hosts
Some sites are set up with a public site (example.com) and an internal site only accessible inside the firewall (app.corp.example.com). When includeSubdomains is set, all sites underneath the specified domain must be accessible over HTTPS, including, in this case, app.corp.example.com. Some corporations have different teams building internal and external applications, and must take care that the security directives applied to the registrable domain are compatible with all of the internal sites running beneath it in the DNS hierarchy. Following the best practices of staged rollout (with gradually escalating max-age directives) will help uncover problems before you brick your internal sites and applications.
Of course, you absolutely should be using HTTPS on all of your internal sites as well, but HTTPS deployments are typically smoother when they haven’t been forced by Priority-Zero downtime.
Mistake: Forgetting Delegated Hosts
Some popular sites and services use third party companies for advertising, analytics, and marketing purposes. To simplify deployments, they’ll delegate handling of a subdomain under their main domain to the vendor providing the service. For instance, www.example.com will point to the company’s own servers, while the hostname mail-tracking.example.com will point to Experian or Marketo servers. A HSTS rule with includeSubdomains applied to example.com will also apply to those delegated domains. If your service provider has not enabled HTTPS support on their servers, all requests to those domains will fail when upgraded to HTTPS. You may need to change service providers entirely in order to unbrick your marketing emails!
Of course, you absolutely should be using HTTPS on all of your third-party apps as well, but HTTPS deployments are typically smoother when they haven’t been forced by Priority-Zero downtime.
Recovery
If you do find yourself in the unfortunate situation of having preloaded a TLD whose subdomains were not quite ready, you can apply for removal from the preload list, but, as noted previously, the removal can be expected to take a very long time to propagate. When a site is removed from the HSTS preload list via HSTSPreload.org, it will take weeks for Chrome and Edge to release the change in their Stable channels, as these removals usually flow through the channels like any other change.
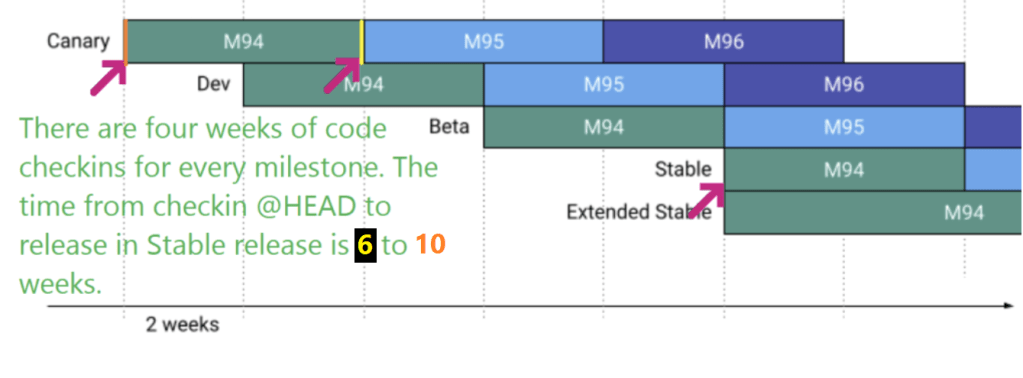
Thus, depending on when exactly the changelist containing the HSTS Preload List Update containing the removal lands, the elapsed time varies: 6 weeks to get to stable if it lands just before the branch for Beta, and ~14 weeks to get to an Extended Stable if it just misses the last one. It could be faster or even slower to get to other browsers which do not pick up the HSTS preload list on the same cadence (e.g. WinINET pulls its preload list from Mozilla’s copy just a few times per year).
For cases where you only have a few domains out of compliance, you should be able to quickly move them to HTTPS. You might also consider putting a HTTPS front-end out in front of your server (e.g. Cloudflare’s free Flexible SSL option) to allow it to be accessed over HTTPS before the backend server is enables HTTPS.
If you’ve broken your Intranet, you might hope that a Group Policy deployed to your employees’ PCs would allow you to turn off HSTS temporarily, but alas, the policy you’re hoping for does not (as of February 2023) exist.
Deploy safely out there!
-Eric