Last Update: February 9, 2024
The new Microsoft Edge offers a rich set of policies that enable IT administrators to control many aspects of its operation.
You can visit edge://policy/ to see the policies in effect in your current browser:

Clicking on a policy name will take you to the documentation for that policy. The Status column indicates whether the policy is in effect, in Error, or Ignored. A policy is in Error if the policy name is unrecognized or the policy value is malformed.
A policy can be Ignored for several reasons. On reason is if the policy is a Protected Policy and the machine is not Domain Joined or MDM managed. Policies are marked “Protected” if they are especially often abused by malware. For instance, policies controlling the content of the New Tab Page are protected because adware/malware commonly attempted to monetize users by silently changing their search engine and homepage when their “free” apps were installed on a user’s PC. Protected Policies are marked in the Edge documentation with the note:
This policy is available only on Windows instances that are joined to a Microsoft Active Directory domain, Windows 10 Pro or Enterprise instances that enrolled for device management, or macOS instances that are that are managed via MDM or joined to a domain via MCX.
When Edge detects that a device is in a managed state in which Protected Policies are allowed, it will show “Managed by your organization” at the bottom of the … menu

A Policy may also be ignored if the user is running in a Personal (MSA) Profile on an Enterprise client and the policy has been filtered as not applicable.
A Policy may also be ignored if there are conflicting policies between EMX/MAM and GP/MDM management tooling.
UPDATE: With the introduction of “Edge for Business” in version 116, some policies apply only to browser profiles signed in with organizational/enterprise accounts (e.g. eric@contoso.com) but not Microsoft Accounts (e.g. eric@hotmail.com). Each of Edge’s available policies has been annotated to note whether it applies to non-organizational accounts. For example, this policy will not be respected for a profile signed in with a personal Hotmail account:
The idea of this split is to better delineate between settings the enterprise is expected to have control over vs. those things that shouldn’t need to be controlled in an employee’s personal browsing. This was an … interesting … design choice.
Implementation mechanism
There’s no magic in how policies are implemented: while you should prefer using edge://policy to look at policies to get Edge’s own perspective about what policies are set, you can also view (and set) policies using the Windows Registry:

On Mac, the policies are stored in a .plist configuration file.
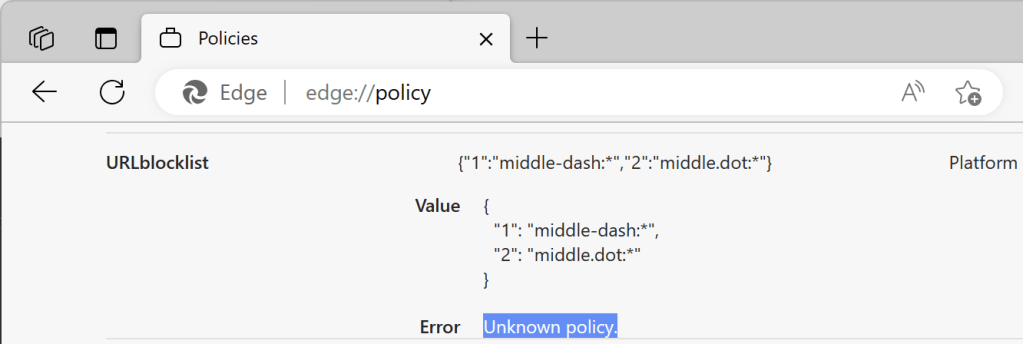
One important note: Chromium policy names are case-sensitive. If you write a policy to the registry yourself (rather than relying on the Group Policy editor or the like), you will see that the policy is not respected if you do not exactly match the case. For example, if you try to specify the URLBlocklist policy but write it as URLblocklist, you’ll see the following error inside the edge://policy page:
Careful, this thing is loaded…
You must take great care when configuring policies, as they are deliberately much more powerful than the options exposed to end-users. In particular, it is possible to set policies that will render the browser and the device it runs on vulnerable to attack from malicious websites.
Administrators should take great care when relaxing security restrictions through policy to avoid opening clients up to attack. For instance, avoid using entries like https://* in URLList permission controls– while such a rule may cover all of your Intranet Zone sites, it also includes any malicious site on the Internet using HTTPS.
… but Incomplete
Notably, not all settings in the browser can be controlled via policy. For instance, some of the web platform feature settings inside edge://settings/content can only be enabled/disabled entirely (instead of on a per-site basis), or may not be controllable by policy at all, only enabling end-user control.
In some cases, you may only be able to use a Master Preferences file to control the initial value for a setting, but the user may later change that value freely.
There’s a ton of great content about managing Edge in the Microsoft Edge Enterprise Documentation, including tables mapping Chrome and Edge Legacy policies to their Edge equivalents.
-Eric