Yesterday, Chris Beard, the CEO of Mozilla, wrote an open letter to Microsoft complaining about Windows 10’s behavior related to default applications. Reactions were all over the board, but in my Twitter feed, at least, they mostly skewed against Mozilla. With the perspective of having been both inside and outside Microsoft, I feel compelled to say a few things.
First, Defaults Matter
Defaults matter. Regardless of its relative merits, the default application is disproportionally likely to get used versus any alternative, even if those alternatives are all free. When I bought my car, it had floor mats— they seem fine; I’m sure they’re not the best floor mats, but I’m going to devote exactly zero thought to replacing them unless they fail me in some way.
It’s no accident that the Edge icon is a little blue “E”—that was the default browser icon for so many years that changing it would’ve been very foolish.
The most compelling argument for the fact that defaults matter is how much gets spent trying to influence them. Most obviously, Microsoft has spent billions in legal settlements and fines related to the default applications on Windows. “But,” you might argue, “that isn’t relevant because they didn’t choose to spend that money.” That’s true, but look at the budget that companies spend to get their software and services distributed and made default. Yahoo, Google, and Microsoft have paid organizations like Mozilla huge sums (on the order of $300,000,000 per year) for over a decade for the opportunity to be the default search engine in Firefox and other browsers.
By way of personal example, around 2010, I was approached with an offer of $1 per install to bundle the Bing Toolbar with Fiddler’s installer in order to increase the number of users defaulted to searching with Bing. I turned down this opportunity (worth somewhere between $300K to $3M per year) because I’m fundamentally opposed to bundling of this sort.
Want to learn more, or prefer your evidence in dead-tree form? Check out Nudge.
“It’s Easy To Change”
Even assuming the user does want to switch to a different browser, any friction in that process impedes change and makes a meaningful difference in adoption. This topic was deeply explored during the Microsoft-E.U. case that led to the browser ballot screen, and every tiny bit of friction was analyzed and negotiated at length. When we were redesigning how ClickOnce worked with IE in Windows 8, we were very constrained by being forbidden to add even a single click to the user flow by which Google Chrome was installed.
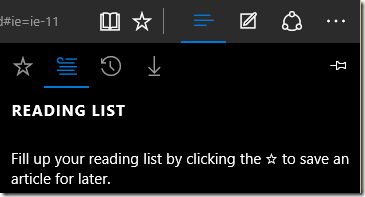
In Windows 8 and Windows 8.1, code was changed in Windows such that (well-behaved) applications could not automatically set themselves as the default handler. Instead, a prompt is shown:
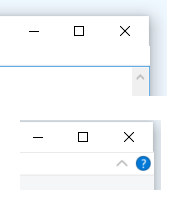
In Windows 10, the same API call yields a very different result:
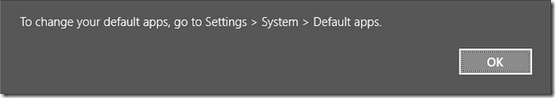
There are a number of significant problems with this. First, it’s not at all clear that this dialog is coming from Windows itself, not the caller, inviting the user to go on a wild goose chase around the app looking for some sort of “Settings” thing. More annoyingly, there’s no “Go there now” button—the computer should serve me, not the other way around. When Picard shouts “Computer: Shields up”, the Enterprise doesn’t reply with “To raise the shields, go to Ship > Controls > Security > Shields.” The omission of an entry point into the experience is glaring to the point of being offensive.
When you get to the “Default apps” controls, how do you change your browser to Chrome or Firefox? Perhaps amazingly, by clicking on Edge:
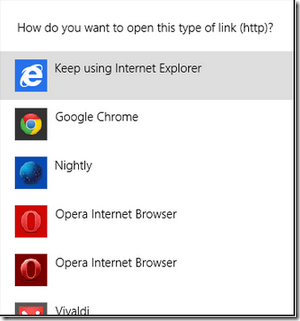
…only then do you see the alternatives:
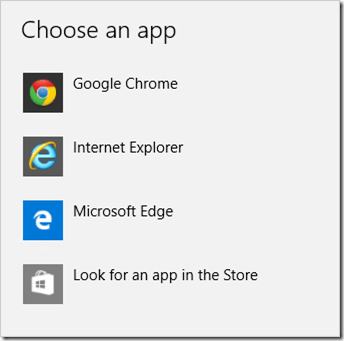
Unfortunately, even if the user makes it all the way here, I think it’s likely to cause problems, and the reason is pretty subtle. In the Windows 8/8.1 UX, the “How do you want to handle this type of link” experience only assigns a “basket” of protocols (HTTP, HTTPS, and maybe FTP) to the selected application. In Windows 10, the “Choose an app” experience appears to give the target all of the protocols it requests. This is a problem, because Google Chrome lists itself as able to handle the mailto: protocol (used for opening email links). But unless you’ve followed some rather obscure steps, Chrome doesn’t actually do anything other than launch when you click a mailto link. So the user experience is bizarrely and confusingly broken.
Claims and Retorts
API Parity
In their blog post announcing the change, Microsoft makes the following (oddly phrased) argument for the change:
In Windows 8.1, Classic Windows applications (Win32) could invoke the prompt asking you to change your defaults, so you may have seen multiple prompts during install and after they launched. However, Windows Store apps could not invoke this prompt.
[…]
We know your defaults matter to you. With Windows 10, all apps – both Classic Windows apps and Universal Windows apps – will be unable to invoke a prompt to change your defaults, only Windows.
Some have leapt to the defense of the change noting that because Store apps couldn’t invoke this prompt, this means that Desktop APIs needed to change. I’d counter that there’s no reason why a similar API couldn’t be exposed for Store apps.
API Deprecation
In the same post, Microsoft notes that applications just need to update their code to avoid the new ugly and unactionable dialog. That’s true as far as it goes– Firefox and Chrome will probably update in their next builds, but this is a problem that could’ve been mitigated in the first place. We know from past experience that requiring applications to change is an adoption hindrance for a new operating system, and there are a long tail of applications which might take a long time to be updated.
What About ABUSE?
Some have argued that this change helps protect users from unwanted changes to their providers, the same argument made for the Windows 8 change. As far as I can tell, no evidence has been provided that the Windows 8 mechanism was ineffective.
“But what about ‘drive-by downloaded’ malware?” some have asked. The first law of computer security is still in effect: a malicious program running at Admin can do anything it likes, including circumventing the speed bumps introduced in Windows 10.
Is Microsoft Evil?
In my twelve years at Microsoft, I can’t recall any cases where anyone sat around twirling their mustache while planning some evil Machiavellian plot. Instead, the problem is that Microsoft too often fails to consider that they are a huge bull and the sole proprietor managing a tightly-packed consignment shop full of china. Any change, regardless of intent, can end up breaking a lot of nice things. For a time, this realization was formalized in the design tenet “Change is bad, unless it’s great.”
Is this Memo A PR Move for Mozilla?
Some commentators are noting that, since other operating systems are even more restrictive in terms of defaults, Mozilla is only complaining about Windows 10 to get attention from the press… as if this were somehow a clever line of argument.
Of course Mozilla is only releasing this complaint now to get attention!
You can’t build a great third-party browser for iOS because of Apple’s lockdowns, and both Google and Mozilla lament this. Mozilla is going so far as to tilt at the windmill of creating their own mobile OS in the hopes of having a shot at relevance in a mobile world. While I liken this to setting fire to a large pit of money and rate its chances of success in the neighborhood of zero, what choice does Mozilla have?
They’re at the mercy of Apple, Google, and Microsoft, companies whose market caps are measured in fractions-of-a-$Trillion USD. Failing to use their bully pulpit as the champion of openness to push back on lockout would represent severe negligence.
Why do I care?
I care because I want the best for Microsoft and I want the best for users. I think Edge is going to become a great browser, and it would be terrible if it were shackled with accusations of dirty tricks in the same way that IE4 and IE5 were, even if the “tricks” aren’t nearly as dirty this time around.
I care because I’m very worried about user-choice. I think Microsoft’s decision to make it much harder for humans to change the default search engine was an awful one and I hope they reverse course. As it stands, Microsoft’s browser share is standing on a precipice—because Edge is exclusive to Windows 10, its share has Windows 10 upgrade adoption shackled to its throat. If Windows 10 lags, Edge might well die with barely a whimper. Similarly, because Edge makes it so hard to switch away from Bing, users who like Edge but find Bing lacking are incentivized to switch to Chrome.
-Eric Lawrence





 Update: Fixed.
Update: Fixed.