Last Updated: 20 May 2024
I’ve previously gushed about the magic of the File Type Policies component — a mechanism that allows files to be classified by their level of “dangerousness”, such that harmless files (e.g. .txt files) can be downloaded freely, whilst potentially-dangerous files (e.g. .dll files) are subjected to a higher degree of vetting and a more security-conscious user-experience.
File Type Danger Level
Microsoft Edge inherits its file type policies from the upstream Chromium browser; you can view the current contents of the list here, and documentation of its format here. UPDATE: As of 2024, Edge’s JSON has evolved significantly from upstream Chromium, and it treats many types as more dangerous than Chrome does.
Within the list, you’ll see that each type has a danger_level, which is one of three values: DANGEROUS, NOT_DANGEROUS, or ALLOW_ON_USER_GESTURE.
The first two danger levels are simple: NOT_DANGEROUS means Safe to download and open, even if the download was accidental. No additional warnings are necessary. DANGEROUS means Always1 warn the user that this file may harm their computer. Let users continue or discard the file. If [SmartScreen or Safe Browsing] returns a SAFE verdict, still warn the user before saving the file.
The third setting, ALLOW_ON_USER_GESTURE2 is more subtle. Such files are potentially dangerous, but likely harmless if the user is familiar with download site and if the download was intentional. Microsoft Edge will allow such downloads to proceed automatically if two conditions are both met:
- User Gesture: There is a user gesture associated with the network request that initiated the download (e.g. the user clicked a link to the download).
- Familiar Initiator: There is a recorded prior visit to the referring origin prior to the most recent midnight (i.e. yesterday or earlier). Such a visit implies that the user has at least some history of visiting the site that kicked off the download.
The download will also proceed automatically if the user explicitly initiated a download by using the Save link as context menu command or entered directly into the browser’s address bar the download’s URL.
SmartScreen/SafeBrowsing Verdict Overrides
Importantly, if Microsoft Defender SmartScreen (in Edge), or Google Safe Browsing (in Chrome), indicates that the file is known safe, that takes precedent over the ALLOW_ON_USER_GESTURE heuristics.
This override allows the user to avoid spurious/scary warnings, for example, when downloading drivers for their graphics card. Without this override, most users would see a warning because the driver installer .exe is served by their GPU vendor’s website (e.g. ati.com) which is somewhat unlikely to be a domain that passes the Familiar Initiator check. Because SmartScreen reports that the signed ATI drivers are non-malicious, it can return a “Safe” verdict and the download will proceed without warning.
I wrote a short blog post about Reputation Services overriding default warnings.
User Experience for Downloads Lacking Gestures
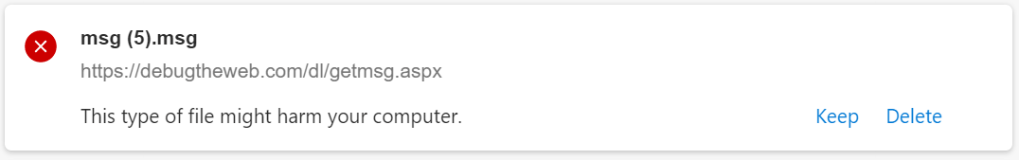
Within Google Chrome, a download lacking a required gesture shows explicit buttons to allow the user to decide whether to proceed with the download or abandon it:
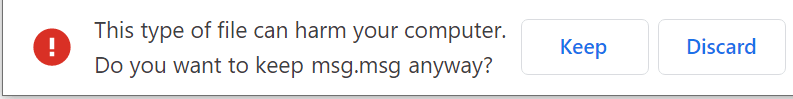
Starting in version 91, Microsoft Edge joined Google Chrome in interrupting downloads that lack the required gesture. However, from Edge 91-94, Microsoft Edge states that the download “was blocked”, although the same options, titled Keep and Delete, are available from the … menu on the download item.

UPDATE: Edge 95+ was updated with an interruption UX more like Chrome’s, in order to better reflect that the user may choose to continue to download the file.
If you visit edge://downloads, you’ll see the same options:
Enterprise Controls
While users are somewhat unlikely to encounter download interruptions for sites they use every day, they might encounter them for legitimate downloads on sites that they use rarely or in sites that hit “Corner Cases” described in a section below.
To help streamline the user-experience for Enterprises, a Group Policy is available.
Enterprises can set a ExemptFileTypeDownloadWarnings policy to specify the filetypes that are allowed to download from specific sites without interruption.
[{"file_extension":"xml","domains":["contoso.com", "woodgrovebank.com"]}, {"file_extension":"msg", "domains": ["*"]}]
If the SmartScreenForTrustedDownloadsEnabled (or equivalent policy for Chrome) is set to 0 (disabled), and the file download’s URL is Trusted (on Windows, in the Local Machine, Intranet, or Trusted zone) then the download will proceed without interruption (even without a gesture), regardless of danger_level. (Aside: This seems a bit strange, but feels more logical if you pretend that the file type warnings are a part of SmartScreen).
File Types Requiring a Gesture
File types policies are published in the Chromium source code. As of May 2021, file types with a danger_level of ALLOW_ON_USER_GESTURE on at least one OS platform include:accda, accdb, accde, accdr, action, ad, ade, adp, apk, app, application, appref-ms, as, asp, asx, bas, bash, bat, caction, cdr, cer, chi, chm, cmd, com, command, configprofile, cpgz, cpi, cpl, crt, crx, csh, dart, dc42, deb, definition, der, desktop, dex, diskcopy42, dmg, dmgpart, dvdr, dylib, efi, eml, exe, fon, fxp, hlp, htt, img, imgpart, inf, ins, internetconnect, inx, isp, isu, job, js, jse, ksh, lnk, mad, maf, mag, mam, maq, mar, mas, mat, mau, mav, maw, mda, mdb, mde, mdt, mdw, mdz, mht, mhtml, mmc, mobileconfig, mpkg, msc, msg, msh, msh1, msh1xml, msh2, msh2xml, mshxml, msi, msp, mst, ndif, networkconnect, ocx, ops, out, oxt, paf, partial, pax, pcd, pet, pif, pkg, pl, plg, prf, prg, ps1, ps1xml, ps2, ps2xml, psc1, psc2, pst, pup, py, pyc, pyo, pyw, rb, reg, rels, rgs, rpm, run, scr, sct, search-ms, service, settingcontent-ms, sh, shar, shb, shs, slk, slp, smi, sparsebundle, sparseimage, svg, tcsh, toast, u3p, udif, vb, vbe, vbs, vbscript, vdx, vsd, vsdm, vsdx, vsmacros, vss, vssm, vssx, vst, vstm, vstx, vsw, vsx, vtx, wflow, workflow, ws, wsc, wsf, wsh, xip, xml, xnk, xrm-ms, xsd, xsl
Note: Microsoft Edge’s file type behaviors may (and as of March 2023, does) diverge from the list of types in upstream Chromium, for security and compatibility reasons.
Other Fields in the File Type Policies
- You’ll also note that some file types have an
auto_open_hintwhich controls whether the user may configure that type of file to open automatically when the download completes. - File type settings sometimes vary depending on the client OS platform (an
.exeis not dangerous on a Mac, while an.applescriptis harmless on Windows). Theplatformattribute of an entry specifies on which OS thedanger_levelapplies. - The
max_file_size_to_analyzefield controls how big of a file (.zip,.rar, etc) the browser will be willing to unpack to scan it for dangerous content.
Group Policies
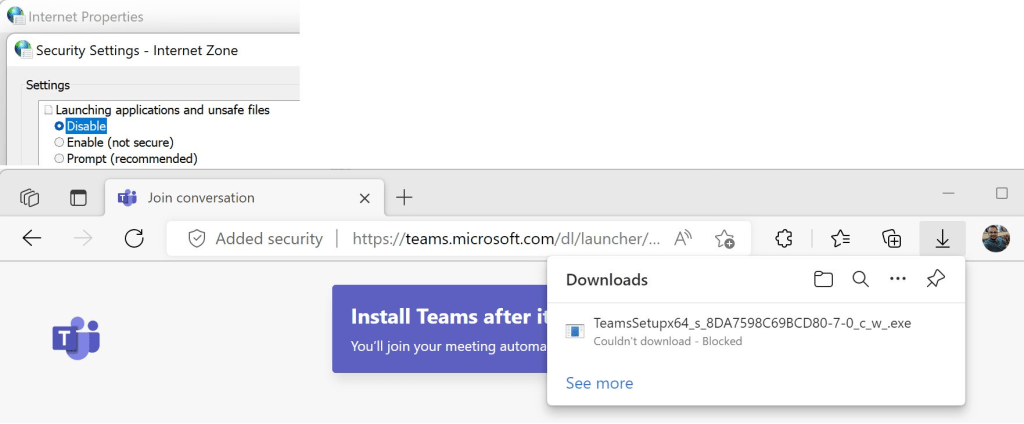
DownloadRestrictions is a policy that makes a complicated browser behavior even more complicated. When you set DownloadRestrictions to 1, Edge won’t just interrupt the download, it will block it.

Make matters even more complicated, if you enable DownloadRestrictions and Disable SmartScreen:
…then the file download is blocked silently with no notice — the Download UX does not show, and no warning is emitted to the Developer Tools console.
Enterprises can use ExemptDomainFileTypePairsFromFileTypeDownloadWarnings to specify the filetypes that are allowed to download from specific sites without blocking.
Corner Cases
- If you put
referrerpolicy="no-referrer"on your download link (or otherwise suppress referrers), the Familiar Initiator check fails. - Prior to v94, if you initiate the download by dynamically creating an
<a>element with adownloadattribute, then click it from JavaScript, the User Gesture check fails.
As of August 2021, Microsoft Outlook Web Access’ email attachment file downloads encounter both of these issues.
Test cases for these conditions can be found here. (Note that you’ll have to have visited webdbg.com yesterday or earlier for the familiarity check to pass).
Surprise: Zones
File download is one of a handful of places where Chromium-based browsers consider Windows security zones.
Beyond the aforementioned impact when the policy SmartScreenForTrustedDownloadsEnabled is set, if you’ve configured a Zone’s setting for Launching applications and unsafe files to Disable using the Windows Internet Control Panel’s Security tab (or the associated Group Policies), Chromium-based browsers will block file downloads from the Zone in question with a terse note: Couldn't download - Blocked.
Update: For version 105, the Chrome team made several significant changes to the file type policies list and behaviors, with the aim of reducing warnings, as seen in this changelist.
-Eric
Appendix: Comparison to other File Type Danger Systems
Microsoft Office maintains its own list of Dangerous File types used in Outlook, Excel, Word, PowerPoint and OneNote.
A Windows Shell API, AssocIsDangerous allows applications to determine whether a given file extension is dangerous according to the system’s registry configuration, which ISVs can extend to describe the danger level of their own file types.
1 DANGEROUS level files are still saved without an explicit warning if the user uses the “Save Link As” command on the browser context menu. Entering the URL via the address bar or command line will still show the warning.
2 ALLOW_ON_USER_GESTURE_AND_FAMILIAR_INITIATOR would be the accurate name for the setting