A colleague recently forwarded me an article about the hazards of browsing on public WiFi with the question: “Doesn’t HTTPS fix this?” And the answer is, “Yes, generally.” As with most interesting questions, however, the complete answer is a bit more complicated. HTTPS is a powerful technology for helping secure the web; all websites should beContinue reading “Understanding the Limitations of HTTPS”
Tag Archives: https
Strict-Transport-Security for *.dev, *.app and more
Some web developers host their pre-production development sites by configuring their DNS such that hostnames ending in .dev point to local servers. Such configurations were not meaningfully impacted when .dev became an official Generic Top Level Domain a few years back, because even as smart people warned that developers should stop squatting on it, Google (the owner of theContinue reading “Strict-Transport-Security for *.dev, *.app and more”
Google Internet Authority G3
For some time now, operating behind the scenes and going mostly unnoticed, Google has been changing the infrastructure used to provide HTTPS certificates for its sites and services. You’ll note that I said mostly. Over the last few months, I’ve periodically encountered complaints from users who try to load a Google site and get an unexpectedContinue reading “Google Internet Authority G3”
Chrome 59 on Mac and TeletexString Fields
Update: This change ended up getting backed out, after it was discovered that it impacted smartcard authentication. Thanks for self-hosting Chrome Dev builds, IT teams! A change quietly went into Chrome 59 that may impact your certificates if they contain non-ASCII characters in a TeletexString field. Specifically, these certificates will fail to validate on Mac, resulting inContinue reading “Chrome 59 on Mac and TeletexString Fields”
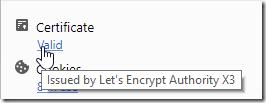
Inspecting Certificates in Chrome
Chrome 60 introduces a new option to quickly show Certificate information for the current page.