By February 7th 2022, I hadn’t yet started jogging on my treadmill, but walking, biking, and improved diet got me down about 15 pounds from my peak.
A year later, I’ve stabilized around forty pounds below that.
ericlaw talks about security, the web, and software in general
On February 11th, 2022, I took my first jog on my new treadmill, a single mile at 5mph. I’d been taking three mile walks for a couple weeks before, but that jog just under a year ago was my first workout over 4mph.
Yesterday, I ran the 3M Half Marathon in Austin, crossing the finish line two hours and forty-six seconds after I started, the culmination of a year’s worth of work.
Going into Sunday’s Half, I had a few worries– the weather was forecast to be cold (in the 30s), and my upper shins and right ankle had been sore for days in places where I’d never hurt before. I went to bed early on Saturday night and woke up at 4am for a few minutes before fortunately dropping back into a deep sleep. Likely with memories of my failed attempt to run the Decker Half, I dreamt that I’d missed joining my pace group and was forced to run alone anyway despite impossible obstacles (e.g. running in the pitch black with no lamp, etc).
In the morning, I felt a bit like I’d had the dream where I was taking a test where I hadn’t studied– lucky that it didn’t really happen but with a renewed commitment to ensuring that it didn’t become real.
Ultimately, I woke up on time feeling pretty good and excited for the run to start, with bib preattached to my shorts, snacks packed, and ready to go. My all-important trip to the bathroom was ultimately unproductive, but I figured that I would get to the start line early enough to have another shot there. There was a fifteen minute line to park, so I didn’t get to the start line until about 15 minutes before the race. It was perhaps 40 degrees, but an intermittently bitter wind made me reconsider my tank top, so I put on the long-sleeve Decker Challenge shirt instead. A quick look at the porta-potty lines suggested that they’d be at least fifteen minutes, so I decided to just find my pace group and stretch a little bit. Fingers crossed.
Five minutes before the start, I nibbled on a GU energy stroopwafel my brother sent me for Christmas as the announcer bantered with the shivering crowd. I started the race in the 1:55 pace group (8:47/mile) based on my Q4 race paces 8:53 (10 miles) and 8:49 paces (5 miles) and my recent treadmill half marathons. Unfortunately, the vibe didn’t really feel right — the pacers were harder to see (shorter, wearing less-bright clothing), and there were clumps of runners around making it awkward to run near them. For lack of better analysis, the energy just didn’t feel right.
I sped up a bit and quickly encountered the 1:50 pace group (8:24/mile). The two pacers were taller, decked out in bright colors, and chatting happily with their group. I ended up happily running the first five miles with them before fatigue started setting in and I decided that I wasn’t going to be able to keep it up.
I slowed down with the hope of keeping the 1:50 group in sight in case I caught my wind, otherwise, at worst, I’d pick up the 1:55 group when they caught up.
Unfortunately, Mile 6 was over a full minute slower than the prior five, and Mile 7’s improved 9:11 pace wouldn’t be seen again until the second half of mile 11. Crossing the 10K mark wasn’t the mental boost I’d expected it to be, and I ended up skipping the tables with GU and goodies at the mid-six mile mark in an attempt to make up some time.
My first 5K was a respectable 25:45, the second was 27:25, and the third took 30:22:
The race is marketed as “Downhill to Downtown” owing to a net 400 foot drop in elevation over the course:
In practice, things are a lot bumpier than the official chart would have you believe:
…and dropping 400 feet over a 69,168 foot race turns out not to be very noticeable on the pavement. But still, the absence of big hills like my recent Run for the Water was definitely appreciated.
Nevertheless, by the time I reached the 9 mile mark, the 1:55 pacers caught and passed me and I got depressed as I found I couldn’t keep up. I consoled myself that my goal was to beat 2 hours and with my fast start, it shouldn’t be too hard to stay ahead of the 2:00 pacers. Still, I was starting to drag on a series of tiny hills. I took half a minute at a porta-potty (after bursting in on someone who’d failed to lock theirs, #awkward) and I started to feel a bit depressed — why was I even running this? While my body was (amazingly) pain free (even my knees and ankle) so far during this run, I knew it was going to ache for days afterward. Even seeing families cheering on the side for their loved ones started to get me down. Still, I got a mental boost when I crossed the 10 mile mark, and by the middle of the 11th mile, I finally felt like I was “in the groove.” Around that time, I ran with the 2:00 pacer for a bit, and in a moment of lucidity I realized I didn’t just need to match the pacer, I needed to beat him, because by starting with the 1:55 group I must’ve crossed the starting line a bit before him.
Alas, my second wind didn’t last, and a series of small hills as we got downtown took the wind out of my sails. In treadmill runs, I typically try to do the last half mile or mile at 7:30/mile, but I just didn’t feel motivated — I was ahead of the pacer, and what was the point? As the spectators multiplied and the end was clearly approaching, I tried not to get my hopes up– it often turns out that there’s another block or two waiting at the end. When I finally crossed the 13 mile marker, I realized that the “end” in sight was really the end, and I sped up as much as was comfortable.
I crossed the finish line in relief and walked to the “results” tables. I figured I’d probably be somewhere in the neighborhood of 1:59:xx… not a big beat, but a beat nonetheless. Through my sunglasses, I had a hard time reading the Chromebook’s screen; I typed my bib number and saw 2:00:46.
What?!? How?!? I beat the pacer by enough that I couldn’t even see him at the end!
It turns out that the 2:00 pacer crossed the finish line just eight seconds after me, but I’d had a whopping 34 second headstart, and he actually finished late, with a time of 2:00:20.
Still happy to be done, I tried to keep my annoyance in check– it wasn’t like I was actually super-close (If I’d missed it by mere seconds, I’d’ve probably been furious), and the reason I wanted to beat two hours was that so I’d never have to run another half, and that didn’t feel so important at the moment. Dejected, I grabbed a swag bag and walked up to the bus line to catch a ride back to the start, without checking out anything else at the finish. Fifteen minutes later, just as we pulled into the parking lot, I realized that everyone else was wearing their medals, and I should at least look at mine, even if I wasn’t going to wear it.
At which point I realized that, contrary to my post-run-delirium assumption, my medal was not, in fact, in the swag bag. Ugh. Perfect. I didn’t want the stupid thing anyway. Except, a quiet voice told me, I kinda did want it. And my friends gave me a fancy rack to show off my race medals, but I don’t have many.
I ended up walking to my car, driving back downtown, and reversing my steps through the corral, back to the finish line, where I grabbed a medal from the previously-overlooked volunteers at the side.
Overall, the entire race was … not what I’d expected. Mentally, I just wasn’t there. If I do ever end up running this far again, I’m going to:
My next run is the Capitol 10K in April; I learned a lot last time, and I’ve trained a lot since then. I’ll aim to cut at least 8 minutes off my prior 67:38 result. Update: I booked another half before then.
-Eric
Postscript: Whelp.
While I have a day job, I’ve been moonlighting as a crimefighting superhero for almost twenty years. No, I’m not a billionaire who dons a rubber bat suit to beat up bad guys– I’m instead flagging phishing websites that try to steal money and personal information from the less tech-savvy among us.
I have had a Hotmail account for over twenty-five years now, and I get a LOT of phishing emails there– at least a few every day. This account turns out to be a great source of real-world threats– the bad guys are (unknowingly) prowling around a police station with lockpicks and crowbars.
When I get a phishing email, I first forward it to Netcraft (scam@netcraft.com) and PhishTank. I copy the URL from the lure, then use the Report > Report Phishing option in Outlook to report the phish to Microsoft:
If I have time, I’ll go look up the URL on URLScan.io and/or VirusTotal to see what they have to say, before loading it into my browser.
Now, most sources will instruct you to never click on a phishing link and this is, in general, great advice. The primary concern is that an attacker might not just be phishing– they might try to exploit a 0-day in your browser to compromise your PC. This is a legitimate concern, but there are ways to mitigate that risk: only use a fully-patched browser, use a Guest profile to mitigate the risk of ambient credential abuse, ensure that you’ve got Enhanced Security mode enabled to block JIT-reliant attacks, and if you’re very concerned, browse using Microsoft Defender AppGuard.
If the phishing site loads (and is not already down or blocked), I then report it to SmartScreen via the ... > Help and feedback > Report unsafe site menu command:
I also report the phishing site to Google’s Chrome/SafeBrowsing team using the Suspicious Site Reporter extension. This extension allows tech-savvy users to recognize suspicious signals for sites they visit and report malicious sites to SafeBrowsing in a single click:
Importantly, the report doesn’t just contain the malicious URL– it also contains information like the Referrer Chain (the list of URLs that caused the malicious page to load), and a Screenshot of the current page (useful for combatting cloaking).
When a user reports a site as phishing, the report typically is sent to a human grader who evaluates the report to determine whether it’s legitimate. The grader typically will load the reported URL to see whether the target meets the criteria for phishing (e.g. is it asking for credentials or credit card numbers and impersonating a legitimate site?).
Phishers do not like it when their websites get blocked quickly.
A technique they use to keep their sites alive longer is named “cloaking.” This technique relies upon detecting that their site has been loaded not by a victim but instead by a grader, and if so, playing innocent– either by returning a generic 404, or by redirecting to some harmless page.
Phishers have many different strategies for detecting graders, including:
Some phishing sites are hosted unintentionally. In these cases, a server is owned by a legitimate company, but bad guys find a vulnerability that allows them to plant content on that server such that it is only shown to specific, targeted victims.
For example, over a decade ago, I received report of an unblocked phishing webpage that was hosted by a hockey rink owner in the US Midwest. My investigation revealed that American visitors to the site would get a normal hockey team signup webpage. However, the phishing campaign was targeting a Russian bank, and if the user visited the site using a browser sending an Accept-Language: ru request header indicating that they spoke Russian, the site would instead serve phishing content. English-speaking graders would never be able to “see” the attack without knowing the “secret” that the site was using to decide whether to serve phishing content. Without screenshots of what a potential victim saw, graders have a very hard time deciding whether a given False Negative report is accurate or not.
Cloaking makes the job of a grader much harder– even if the reporter can go back to the grader with additional evidence, the delay in doing so could be hours, which is often the upper-limit of a phishing site’s lifetime anyway.
If you want to learn even more ways to combat phishing sites, check out the guide at GotPhish.com.
For example, Netcraft also offers a browser extension that shows data about the current website and allows easy reporting of phish:
If doing a good deed isn’t enough, Netcraft also offers some fun incentives for phishing reports— so far, I’ve collected the flash drive, mug, and t-shirt.
One criticism against adding advanced features to browsers to allow analysis or recognition of phishing sites is that the vast majority of users will not be able to make effective use of them. For instance, features like domain highlighting (showing the eTLD+1 in bold text) are meaningless to 99% of users.
But critically, such cues and signals like these are useful to experts, who can recognize the signs of a phish and “pull the alarm” to report phishing sites to SmartScreen, SafeBrowsing, and other threat intel services.
These threat reports, consumed by threat intelligence services, then scale up to “protect the herd.” Browsers’ blocking pages for known phish are demonstrably extremely effective, with high adherence even by novice users.
Now, it’s easy to wonder whether or not any of this end-user reporting matters — there are millions of new phish a week — can reporting one make a difference?
Beyond my immediate answer (yes), I have personal evidence of the impact. One of my happiest memories of working on the IE team was when the SmartScreen team looked up how many potential victims my phish reports blocked. I shared with them my private reporter ID and they looked up my phishing reports in the backend, then cross-referenced how many phishing blocks resulted from those reports. The number was well into the thousands.
Beyond the immediate blocks, threat reports these days are also used by researchers to identify phishing toolkits and campaigns, and new techniques phishers are adopting. Threat reports are fed into AI/ML models and used to train automatic detection of future campaigns, making the life of phishers more difficult and less profitable.
Thanks for your help in protecting everyone!
-Eric
While I’m best known for creating Fiddler two decades ago, eight years before Fiddler’s debut I started work on what became SlickRun. SlickRun is a floating command line that provides nearly instant access to almost any app or website. Originally written in Visual Basic 3 and released as QuickRun for Windows 3.1, it was soon ported to Borland Delphi and later renamed SlickRun to avoid a name-collision with an unrelated tool.
SlickRun was a part of the story of how I joined Microsoft — when I had my on-campus interview for my first internship, I’d brought a binder of screenshots from apps that I’d written. My interviewer was generally interested but got super-excited as I explained what SlickRun did. “Have you shown this to Microsoft??” he asked. Flummoxed and wondering Uh, how exactly would I have done that?, I replied “Uh, I guess I just did?” Five years later when I interviewed for the IE team, the GM interviewing me asked “How often do you type www.goo in the browser address bar and wish it did the right thing?” to which I responded “Uh, less than you might think.” before showing off the autocomplete inside SlickRun. I got that job too.
While I’ve maintained SlickRun routinely over the years, making updates as needed to support 32bit, and then 64bit Windows, and keep it compatible with new paradigms in Windows Vista and beyond, I’ve done relatively little to publicize it to the world at large. It just quietly hums along with a mostly-satisfied userbase of thousands around the world.
Personally, I’ve been using SlickRun nearly daily for almost three decades and have executed almost 200000 commands on my latest fleet of Windows 11 PCs.
Perhaps the biggest problem with SlickRun is that, designed to be small and simple, it offers few affordances to reveal the tremendous amount of power living under the surface. By default, it ships with only a handful of MagicWords (command shortcuts/aliases) but it will never achieve its full power unless the user creates their own MagicWords to match their own needs and terminology.
If a user types HELP, an online help page will open to explain the basics, and for the few who bother to read that page, an advanced usage page reveals some even less obvious features of the tool.
I’ve been meaning to put together a demo reel video for decades now but have never gotten around to it. Mostly, SlickRun has spread organically, with folks seeing it in use on a peer’s desktop and asking “Hey, how … what is that?”
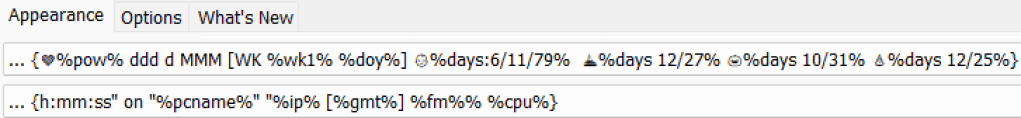
Beyond its program-launching features, SlickRun provides a useful little perch for showing information in an always-visible (by default) location on your desktop. If you type SETUP, there’s a variety of display customization options. SlickRun’s “idle” appearance which can show useful things like clocks (in arbitrary time zones), date, battery life, days-until-an-event, machine name, IP address, memory usage, CPU usage, etc:
If SlickRun ever gets in your way (e.g. while watching a full-screen video), just type HIDE to tell it to hide out in your system tray until summoned.
Click on SlickRun or hit the hotkey to activate it and enter command mode. (The hotkey is configurable via SETUP. For historical reasons, it defaults to Win+Q which doesn’t work on modern Windows without a simple registry modification due to other tools camping on that key. After a decade, I configured mine to Alt+Q instead.)
Type a command into SlickRun and hit enter to launch it. You can hit the tab key to jump to the end of an autocomplete suggestion if you want to change or add arguments at the end of the command.
Use the up/down arrow keys to scroll through your command history– if you’ve already typed some characters, the history is filtered to just the commands that match. Or hit Alt+F to show a context menu list of all matches (or ALT+Shift+F to loosen the matching to the entire command, not just the prefix). Or, hit Alt+S to show a context menu list containing any Start Menu shortcuts containing what you’ve already typed.
SlickRun loves the internet. Type a url in SlickRun to open it in your default browser. My very favorite MagicWord launches an “I’m Feeling Lucky” Search on Google, so I can type goto SlickRun and https://bayden.com/slickrun/ will open (see this post for more info). This works magically well.
As you can see, you can add MagicWords to launch web searches, where $W$ is filled by a URL-encoded parameter. For example:

After creating this MagicWord, you can type errors 0x1234 and your browser will go to the relevant URL. If you fail to specify a parameter when invoking the MagicWord, you’ll be asked to supply it via a popup window:
You can type CALENDAR to launch a calendar, or CALENDAR 5/6 to jump to May sixth.
Using @MULTI@, you can have a single MagicWord launch multiple commands:
In cases where you have related commands, you can name your MagicWords with a slash in the middle of them; each tab of the tab key will jump to the next slash, allowing you to adjust what is autocompleted as you go.
So, for example, I can type e.g. e{tab}s to get to “Edge Stable” in the autocomplete:

When executing a MagicWord, a $C$ token will replaced by any text found on the clipboard.
Hit Ctrl+I to get a Windows file picker to insert a file path at the current location of the command line string. Or, tap Ctrl+V with one or more files on your clipboard and SlickRun will insert the file path(s) at the current insertion point. Hit Ctrl+T to transpose the last two arguments in the current command (e.g. windiff A B becomes windiff B A) and hit CTRL+\ to convert any Unix-style path separator backslashes (c/src/chrome/) into Windows-style backslashes (c\src\chrome\).
SlickRun can perform simple math operations, with the answer output inline such that you can chain it to a subsequent operation. Try things like
=2^9
=SQR(100)
=123*456
=0x123
=HEX(123)
When running a command, use Shift+Enter to execute a command that should be immediately forgotten. Use Ctrl+Shift+Enter to execute a command elevated (as administrator).
You can create a MagicWord named _a which will execute any time you hit ALT+Enter to submit a command, so the following MagicWord allows you to look up a word by typing define powerful or ?powerful or just typing powerful and submitting via Alt+Enter:
If you name your MagicWord _default, SlickRun will execute it if no other command is found.
You can use SETUP to configure an hourly chime with an optional offset so you’ll have a minute or more to get ready for your next meeting or appointment:
A MagicWord named _STARTUP will be run automatically anytime SlickRun starts. A MagicWord named _DISPLAYCHANGE will run automatically anytime your Windows display resolution changes.
SlickRun flashes when your clipboard is updated, useful for confirming that your attempt to copy something from another app was successful.
You can create a MagicWord with the @copy@ command to copy a string to your clipboard, useful if you have a string that you need to use frequently.
You can drag/drop URLs from webpages, or icons from Start/Desktop to create MagicWords pointing to them.
Hit Ctrl+V with one or more files on your clipboard and SlickRun will insert the file path(s) at the current insertion point.
You can drag/drop text from anywhere to SlickRun to add it to your JOT, an auto-saving jotpad, useful for recording addresses, phone numbers, order confirmation numbers, and the like. Type JOT to reopen it later.
Every tool has its limits, and SlickRun is no exception. There are a bunch of features that I’d like to add, but I haven’t gotten around to over the decades.
The most often noticed shortcoming is that SlickRun doesn’t offer roaming for features you’d hope (in particular, the MagicWord list and the text of the JOT). Unfortunately, it’s non-trivial, and while you can import/export your command library, you cannot trivially use OneDrive or Google Drive to keep a single command library in sync.
I’ve always daydreamed about adding “natural” language recognition to SlickRun (including voice recognition) but I’ve never made any significant effort to explore it, even as technology has advanced to the point where doing so might now be very practical. (LLVMs like ChatGPT are an obvious integration).
SlickRun should be open-source, but the code is in a language (Delphi/Object Pascal) which is uncommon. While the code works, it’s not of quality that I would be proud for anyone to see. In the early years, I had a collaborator who wrote the performance critical auto-complete logic, but in twenty years since, only I have lain eyes on SlickRun’s mostly crusty code. I periodically ponder an OSS rewrite in C# (someone else did this as a short-lived project named “MagicWords”) but haven’t found the energy. Fiddler users might recognize that tool’s QuickExec box‘s origins in SlickRun– I partly added QuickExec to Fiddler in the hopes that one day I’d find that I’d added so much functionality to it that I could fork that code out into a SlickRun.NET. Alas, that didn’t happen by the time Telerik acquired Fiddler.
I hope you find SlickRun useful!
-Eric
I spent dramatically more time on physical fitness in 2022 than I have at any other point in my life, in preparation for my planned adventure this June.
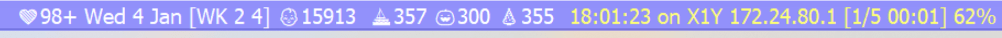
My 2022 statistics from iFit on my incline trainer/treadmill show that I walked/jogged/ran almost 700 miles after it was set up on January 24th:
Perhaps surprisingly (given the summer heat), I got the most miles in over the summer months:

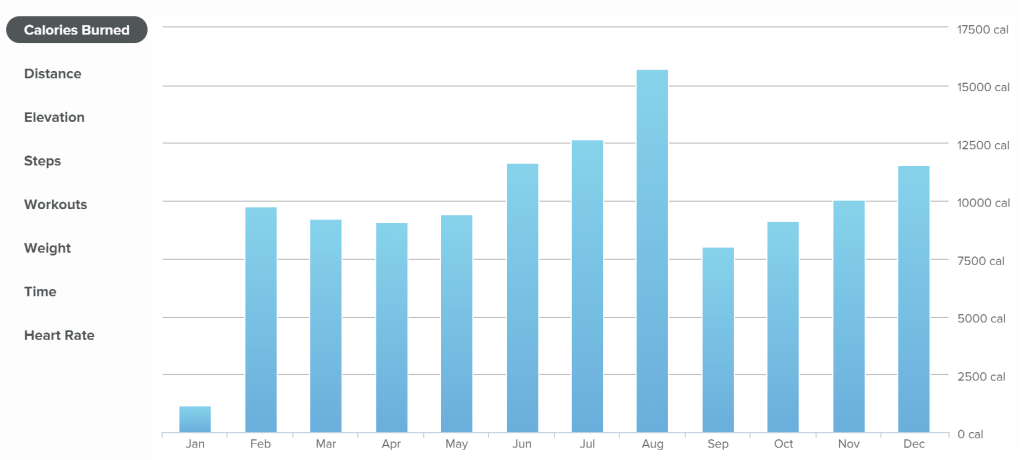
Beyond the treadmill, I also ran a few real-world races. Compared to the first half, my use of the exercise bike declined in the latter half of the year, but I still rode a few times a month:

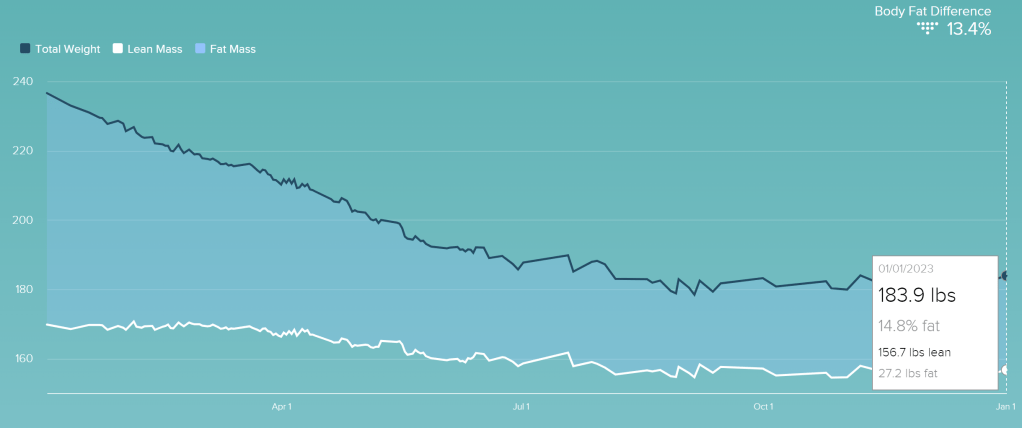
I ended the year 52.7 pounds lighter than I started it, bottoming out at 178.4 pounds in early September before rebounding a bit in the final months of the year. My estimated body fat percentage dropped from a peak of 28.9% to just under 15%.
My FitBit reports 4,186,894 steps, 3184 floors, 2181.91 miles and 1,183,581 calories burned:

My resting heart rate dropped from 64 to 54 beats per minute in the first third of the year, and has bounced around by a beat or two over the rest of the year. I haven’t checked my blood pressure regularly since noting a big improvement in the first third of the year. I got my fourth COVID shot before a second COVID infection in September– I shrugged it off easily in a week.
I’ve got a real-world half marathon (3M) coming up in just over a week, then the Austin Capital 10K coming in April. Then, hiking Kilimanjaro in June.
After that, I’m not sure what’s next: right now, I expect to cut back on running distances to stay around 10Ks, and hope I’ll be able to force myself to start using the rower regularly.
I’m doing another “Dry January” this year. My experiment with alcohol-free beer (Athletic Brewing Company) is a mixed bag– it tastes “fine“, but triggers the same munchies that “real” beer does, which rather limits the point of the exercise. I tried an alcohol-free liquor (“Spirit of Milano“) but I really don’t like it– I’ll stick to cranberry juice.