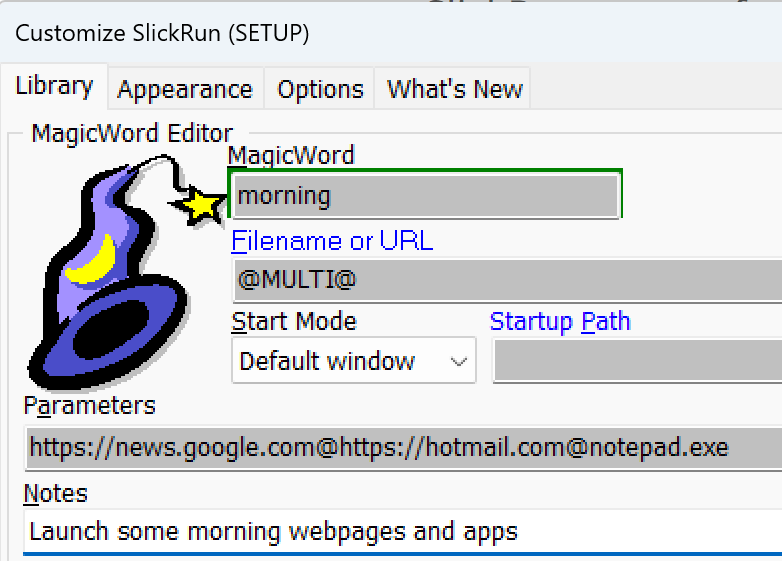
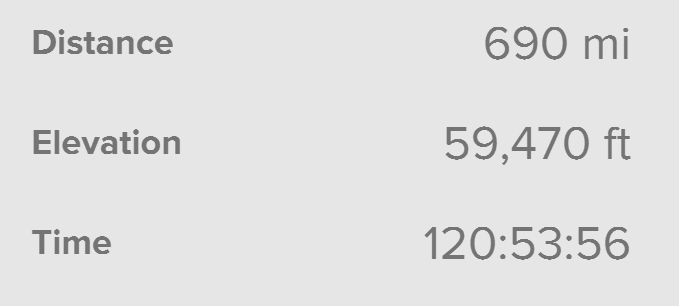
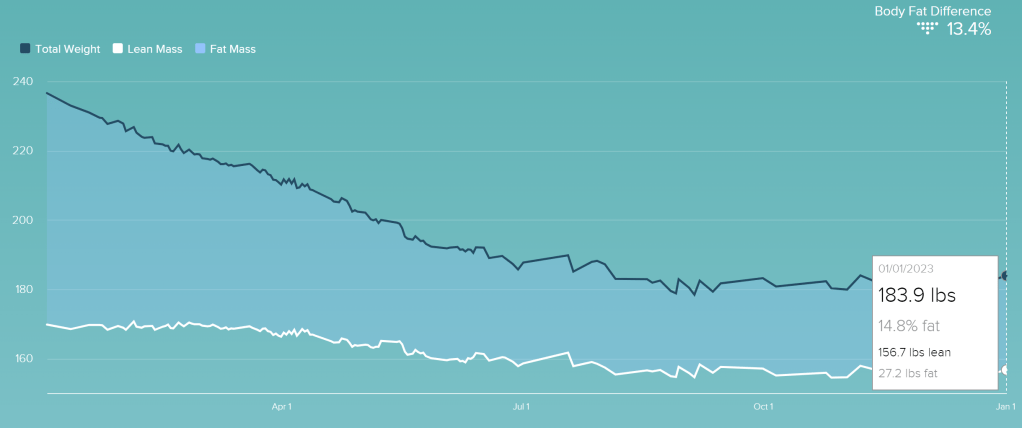
On February 11th, 2022, I took my first jog on my new treadmill, a single mile at 5mph. I’d been taking three mile walks for a couple weeks before, but that jog just under a year ago was my first workout over 4mph.
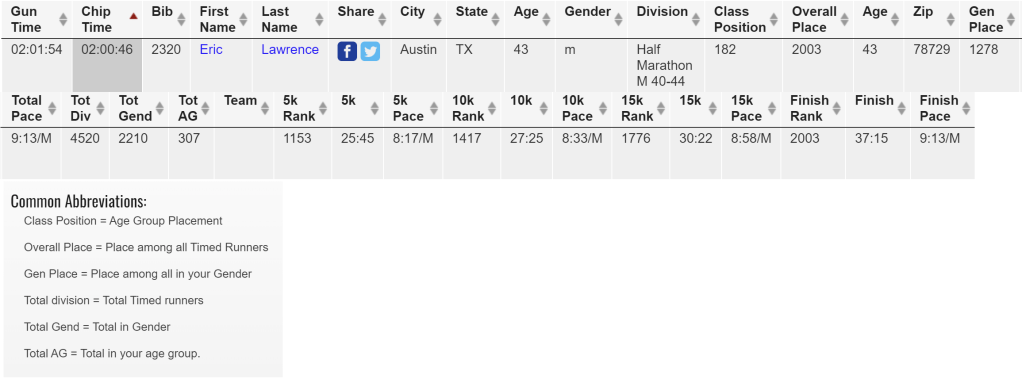
Yesterday, I ran the 3M Half Marathon in Austin, crossing the finish line two hours and forty-six seconds after I started, the culmination of a year’s worth of work.
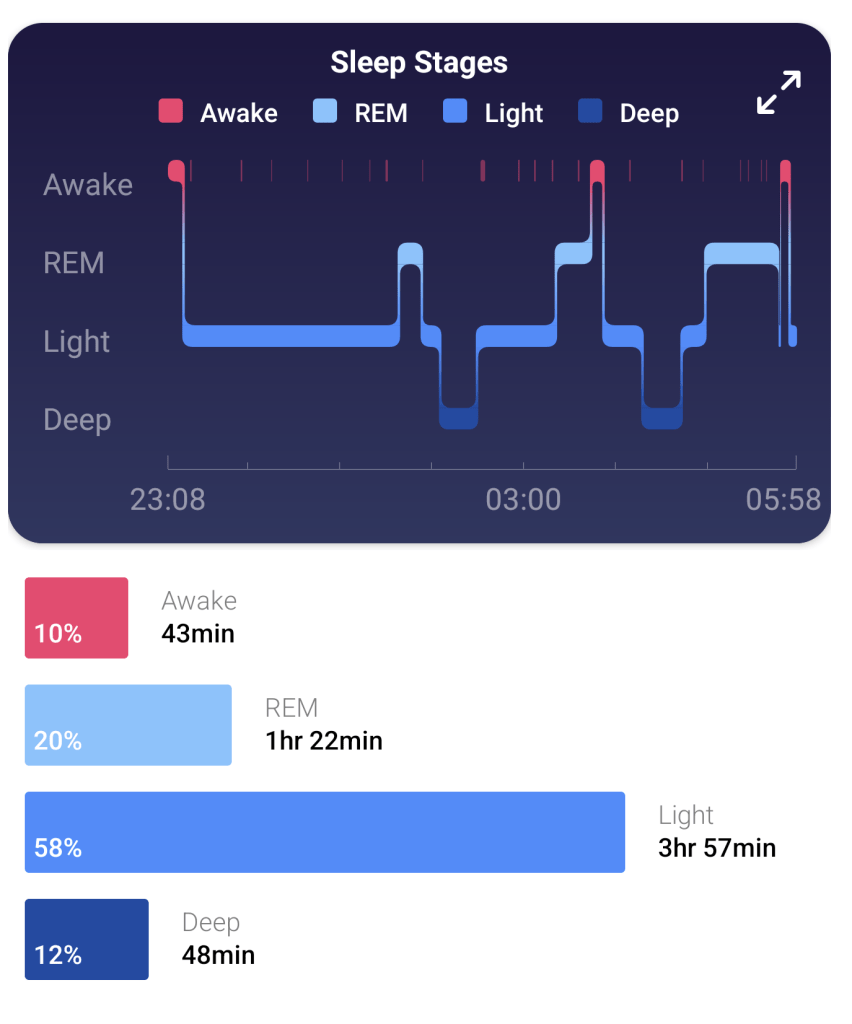
Going into Sunday’s Half, I had a few worries– the weather was forecast to be cold (in the 30s), and my upper shins and right ankle had been sore for days in places where I’d never hurt before. I went to bed early on Saturday night and woke up at 4am for a few minutes before fortunately dropping back into a deep sleep. Likely with memories of my failed attempt to run the Decker Half, I dreamt that I’d missed joining my pace group and was forced to run alone anyway despite impossible obstacles (e.g. running in the pitch black with no lamp, etc).
In the morning, I felt a bit like I’d had the dream where I was taking a test where I hadn’t studied– lucky that it didn’t really happen but with a renewed commitment to ensuring that it didn’t become real.
Ultimately, I woke up on time feeling pretty good and excited for the run to start, with bib preattached to my shorts, snacks packed, and ready to go. My all-important trip to the bathroom was ultimately unproductive, but I figured that I would get to the start line early enough to have another shot there. There was a fifteen minute line to park, so I didn’t get to the start line until about 15 minutes before the race. It was perhaps 40 degrees, but an intermittently bitter wind made me reconsider my tank top, so I put on the long-sleeve Decker Challenge shirt instead. A quick look at the porta-potty lines suggested that they’d be at least fifteen minutes, so I decided to just find my pace group and stretch a little bit. Fingers crossed.
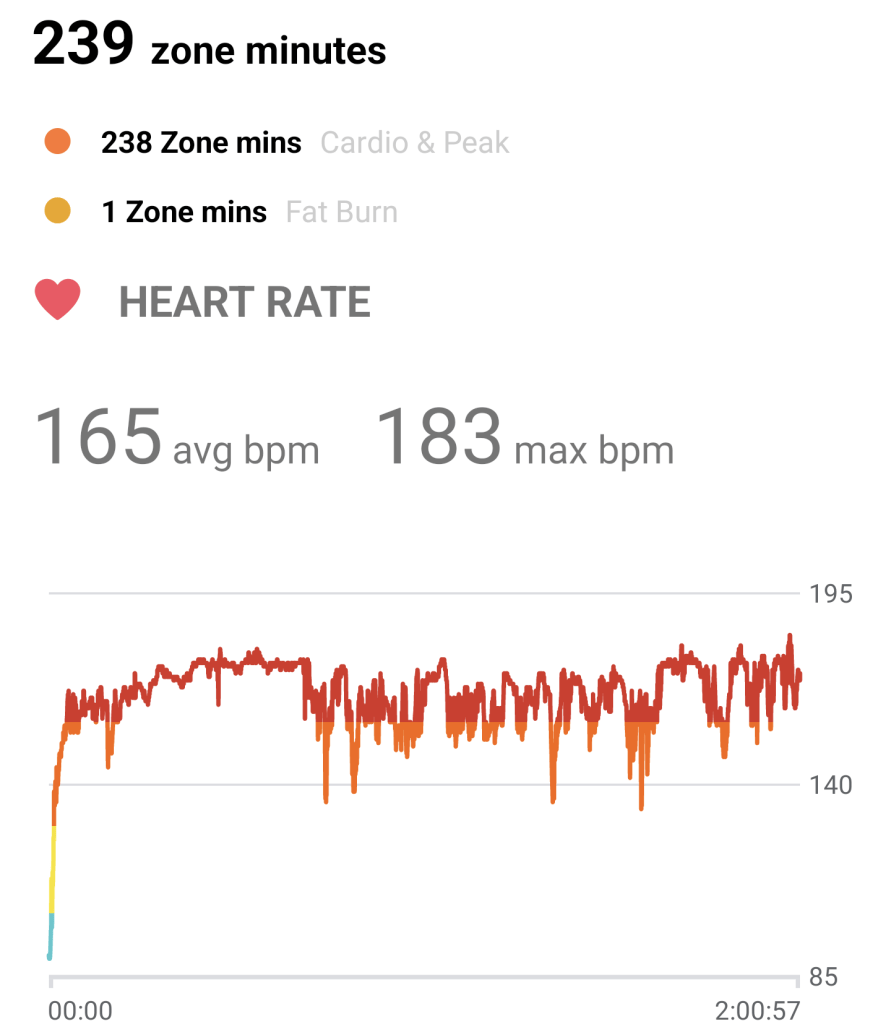
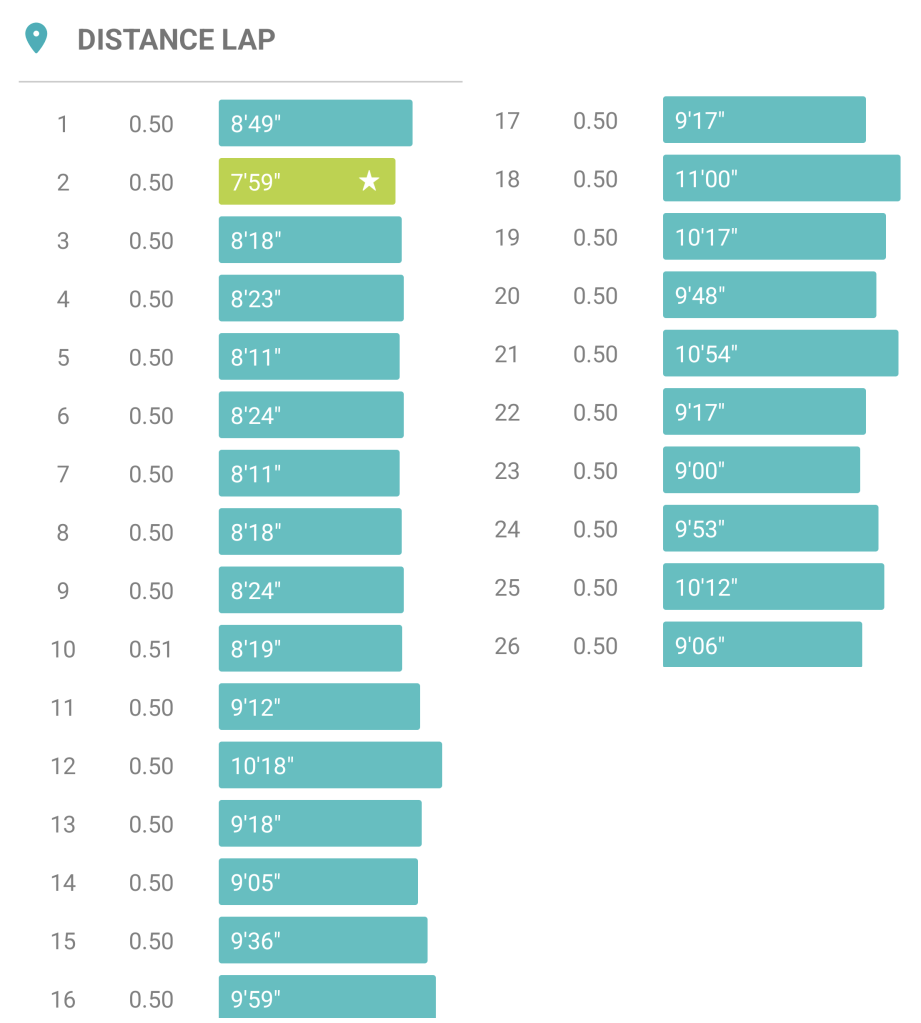
Five minutes before the start, I nibbled on a GU energy stroopwafel my brother sent me for Christmas as the announcer bantered with the shivering crowd. I started the race in the 1:55 pace group (8:47/mile) based on my Q4 race paces 8:53 (10 miles) and 8:49 paces (5 miles) and my recent treadmill half marathons. Unfortunately, the vibe didn’t really feel right — the pacers were harder to see (shorter, wearing less-bright clothing), and there were clumps of runners around making it awkward to run near them. For lack of better analysis, the energy just didn’t feel right.
I sped up a bit and quickly encountered the 1:50 pace group (8:24/mile). The two pacers were taller, decked out in bright colors, and chatting happily with their group. I ended up happily running the first five miles with them before fatigue started setting in and I decided that I wasn’t going to be able to keep it up.
I slowed down with the hope of keeping the 1:50 group in sight in case I caught my wind, otherwise, at worst, I’d pick up the 1:55 group when they caught up.
Unfortunately, Mile 6 was over a full minute slower than the prior five, and Mile 7’s improved 9:11 pace wouldn’t be seen again until the second half of mile 11. Crossing the 10K mark wasn’t the mental boost I’d expected it to be, and I ended up skipping the tables with GU and goodies at the mid-six mile mark in an attempt to make up some time.
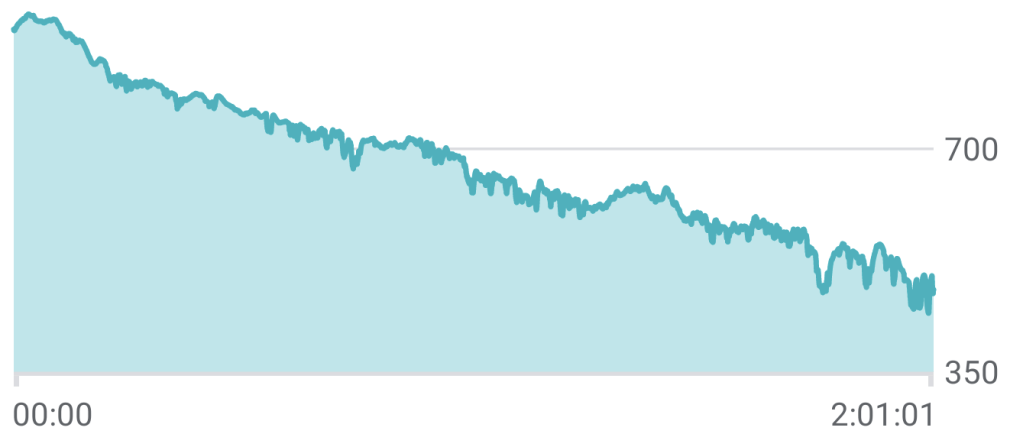
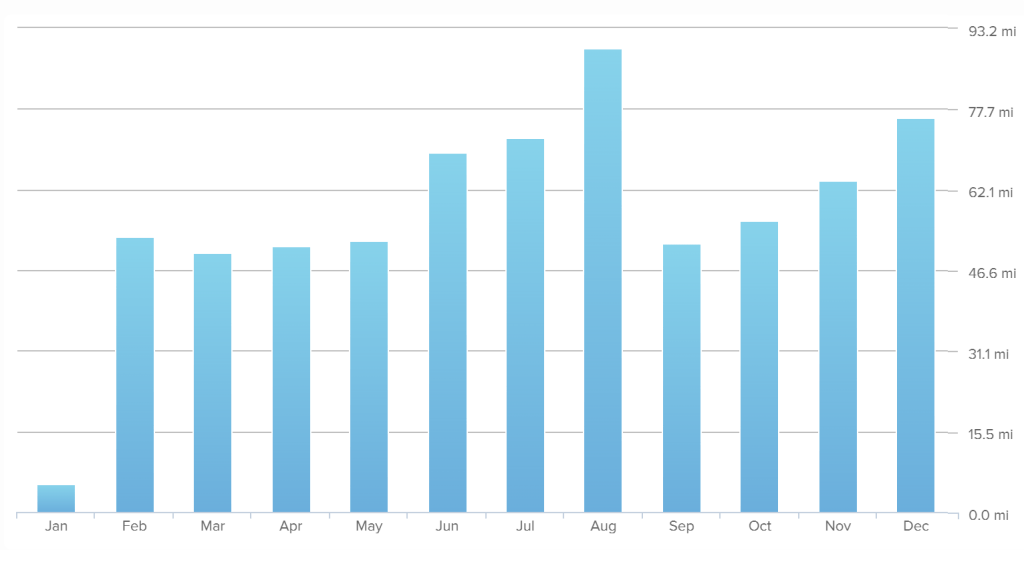
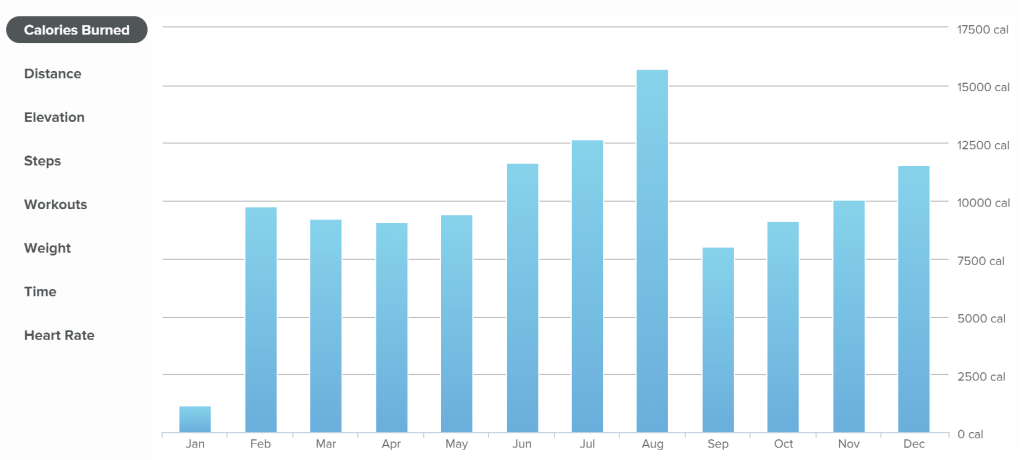
My first 5K was a respectable 25:45, the second was 27:25, and the third took 30:22:
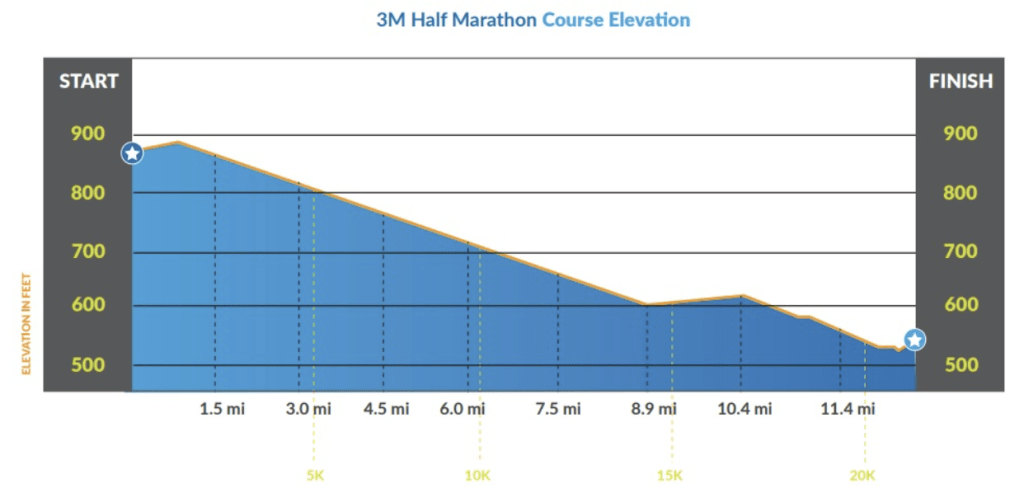
The race is marketed as “Downhill to Downtown” owing to a net 400 foot drop in elevation over the course:
In practice, things are a lot bumpier than the official chart would have you believe:
…and dropping 400 feet over a 69,168 foot race turns out not to be very noticeable on the pavement. But still, the absence of big hills like my recent Run for the Water was definitely appreciated.
Nevertheless, by the time I reached the 9 mile mark, the 1:55 pacers caught and passed me and I got depressed as I found I couldn’t keep up. I consoled myself that my goal was to beat 2 hours and with my fast start, it shouldn’t be too hard to stay ahead of the 2:00 pacers. Still, I was starting to drag on a series of tiny hills. I took half a minute at a porta-potty (after bursting in on someone who’d failed to lock theirs, #awkward) and I started to feel a bit depressed — why was I even running this? While my body was (amazingly) pain free (even my knees and ankle) so far during this run, I knew it was going to ache for days afterward. Even seeing families cheering on the side for their loved ones started to get me down. Still, I got a mental boost when I crossed the 10 mile mark, and by the middle of the 11th mile, I finally felt like I was “in the groove.” Around that time, I ran with the 2:00 pacer for a bit, and in a moment of lucidity I realized I didn’t just need to match the pacer, I needed to beat him, because by starting with the 1:55 group I must’ve crossed the starting line a bit before him.
Alas, my second wind didn’t last, and a series of small hills as we got downtown took the wind out of my sails. In treadmill runs, I typically try to do the last half mile or mile at 7:30/mile, but I just didn’t feel motivated — I was ahead of the pacer, and what was the point? As the spectators multiplied and the end was clearly approaching, I tried not to get my hopes up– it often turns out that there’s another block or two waiting at the end. When I finally crossed the 13 mile marker, I realized that the “end” in sight was really the end, and I sped up as much as was comfortable.
I crossed the finish line in relief and walked to the “results” tables. I figured I’d probably be somewhere in the neighborhood of 1:59:xx… not a big beat, but a beat nonetheless. Through my sunglasses, I had a hard time reading the Chromebook’s screen; I typed my bib number and saw 2:00:46.
What?!? How?!? I beat the pacer by enough that I couldn’t even see him at the end!
It turns out that the 2:00 pacer crossed the finish line just eight seconds after me, but I’d had a whopping 34 second headstart, and he actually finished late, with a time of 2:00:20.
Still happy to be done, I tried to keep my annoyance in check– it wasn’t like I was actually super-close (If I’d missed it by mere seconds, I’d’ve probably been furious), and the reason I wanted to beat two hours was that so I’d never have to run another half, and that didn’t feel so important at the moment. Dejected, I grabbed a swag bag and walked up to the bus line to catch a ride back to the start, without checking out anything else at the finish. Fifteen minutes later, just as we pulled into the parking lot, I realized that everyone else was wearing their medals, and I should at least look at mine, even if I wasn’t going to wear it.
At which point I realized that, contrary to my post-run-delirium assumption, my medal was not, in fact, in the swag bag. Ugh. Perfect. I didn’t want the stupid thing anyway. Except, a quiet voice told me, I kinda did want it. And my friends gave me a fancy rack to show off my race medals, but I don’t have many.
I ended up walking to my car, driving back downtown, and reversing my steps through the corral, back to the finish line, where I grabbed a medal from the previously-overlooked volunteers at the side.
Overall, the entire race was … not what I’d expected. Mentally, I just wasn’t there. If I do ever end up running this far again, I’m going to:
- Start at a more sustainable pace
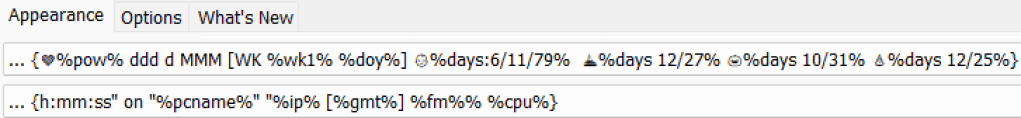
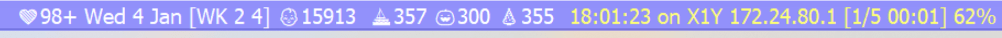
- Have a watch that’s more useful (mine is hard to read with sunglasses, and as configured, it makes it too hard to see elapsed time and distance)
- Make sure I’ve got good music on my playlist (I had music I liked, but a bunch of it is not what I’d consider “running music”)
My next run is the Capitol 10K in April; I learned a lot last time, and I’ve trained a lot since then. I’ll aim to cut at least 8 minutes off my prior 67:38 result. Update: I booked another half before then.
-Eric
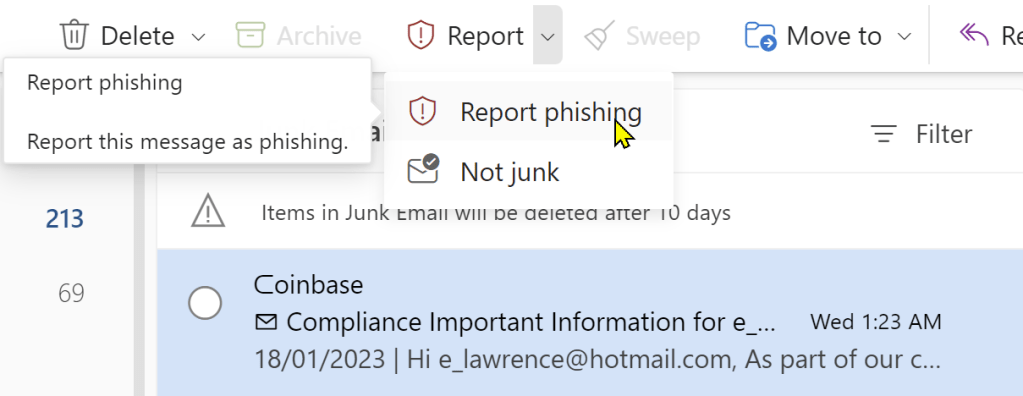
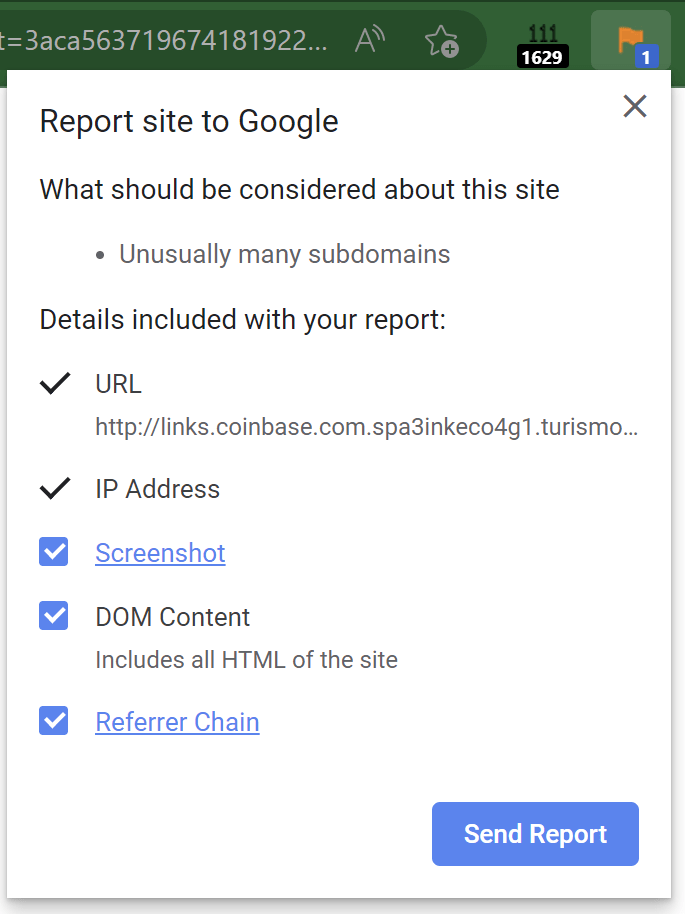
Postscript: Whelp.